Technology
ISSAN Seeks Collaborative Efforts to Check Rising Cyber Threats

By Modupe Gbadeyanka
An urgent review of the National Cybersecurity Protection Act of 2015 has been called for by the Information Security Society of Africa, Nigeria (ISSAN).
According to the cybersecurity stakeholders, the review will make the law meet the current realities as it will capture the latest trends in the industry.
Speaking at the Quarter 1, 2022 ISSAN Cybersecurity Conference themed Payment Systems Platform Security in Lagos, the president of ISSAN, Dr David Isiavwe, said as the COVID-19 pandemic is gradually easing out, organisations are now settling for a hybrid way of working and providing services for customers while being mindful of the enlarged cyber threat.
He noted that new forms of attacks are being contrived and implemented by criminals through various means on individuals, nation-states and corporate bodies, stressing that cyber security gatekeepers are not spared as large sums of money are usually at risk in every successful attack.
“What we see on the horizon is that Business Email Compromise (BEC) attacks are becoming alarming; Ransomware attacks are not relenting. There are more phishing and password targeted attacks.
“Denial of Service (DoS) and Distributed Denial-of-Service (DDoS) attacks remain a growing problem. The loss globally is colossal. In Africa, Nigeria is expected to lead in terms of estimated loss due to our size. There is, therefore, the urgent need to brainstorm on how to keep payment systems platforms safer,” he said.
For a way forward, Dr Isiavwe, who is also a General Manager at Ecobank Nigeria, emphasised that banks and organisations need to be proactive, keep customers educated and updated on new threats and trends in cyberspace, automate and continuously monitor their systems and infrastructure, and also place a high premium on artificial intelligence, machine learning, robotics, and data analytics.
In his keynote address, Director, Payment System Management Department, Central Bank of Nigeria (CBN), Mr Musa Jimoh commended the activities of ISSAN on enhancing a safer and secured payment ecosystem, stressing that the apex bank is committed to initiatives that would promote and enhance payment system security to check cyber fraud in the nation’s financial system.
He maintained that the financial sector cannot afford to fail as the payment system is vital to the functioning of any economic system.
According to him, “Data security is important for customers and a tool for financial inclusion. Banks are the custodian of customers’ information based on trust and should therefore put structures in place to prevent breaches and information theft. They should not compromise customers’ credentials as it would give cybercriminals access to defraud them.”
Mr Jimoh further stated that the entrance of Fintechs to the financial landscape has engendered stiffer competition, noting that “all responsible officers in charge of information security in organizations should keep track and always check and see the right things are done for the entities that are allowed to connect to their infrastructure.
“Banks should address infrastructure deficiencies, ensure operational resilience, introduce second or multi-factor authorisation, ensures banking payment infrastructure are formidable, address privacy violations, carry out end to end encryption to protect stored data, and also adhere to KYC provisions to avoid terrorism financing and money laundering.”
In her technical presentation, Managing Director, CreditRegistry Plc, Dr Jameela Ayedun, recommended a collaborative approach by banks, CBN, government agencies such as National Identity Management Commission (NIMC), Nigerian Communications Commission (NCC), Nigeria Inter-Bank Settlement System (NIBSS) and others to enhance cyber security.
According to her, “Cyber security is the responsibility of all. The cybercriminals are still on a rampage therefore we must protect our payment systems and not give anything to chance.
“We must educate our consumers and should not be a silent victim. The payment service providers must have the basic requirements. The government also has a role to play in this regard. We should emphasise the privacy and integrity of our payment systems.”
Also, in his technical presentation titled: Anatomy of the New Fraudsters – A Nigeria Perspective, Head, Growth and Partnership – West Africa, BPC Technologies, Emmanuel Obinne, observed that cyber frauds transcend borders and boundaries. He gave a rundown of different types of frauds and maintained that relevant cyber laws should be put in place to check cyber criminality.
According to him, “Fraud management is a journey and not a destination. Proper laws should be in place to punish cybercriminals. Organizations should regularly upgrade their payment systems and security to avoid vulnerability. This will also fast track authorization and authentication of transactions. Second-factor authorization is also important to check fraud. The customers must constantly be educated to make them have more confidence in the payment system.”
Other panellists at the hybrid summit were Chairman, Association of Chief Audit Executives of Banks in Nigeria (ACAEBIN), Yinka Tiamiyu; Chief Information Security Officer, Heritage Bank, Ighoakpo Eduje, and Managing Partner, Technology Advisors LLP, Basil Udotai. The session was moderated by the Head, Internal Audit, FBN Holdings, Dr Bode Oguntoke.
Technology
Why Simplicity Now Beats Bigger Motion Suites
Most people do not go looking for motion tools because they love software. They go looking because they already have an image that feels unfinished. It might be a portrait that needs movement, a product shot that needs more energy, or a still frame that needs to become a short social clip. That is why Image to Video AI stood out to me more than many broader video platforms. In this category, the real question is not whether AI can animate an image. The real question is whether it can do so in a way that feels understandable, practical, and repeatable.
A lot of rankings in this space reward spectacle. They favor the system that produces the wildest sample or the most cinematic first impression. That can be fun, but it is not always helpful. In my testing, usefulness came from something less glamorous: how quickly a platform helped me move from a single still image to a result I could actually imagine publishing, refining, or repurposing. When I looked at seven well-known image-to-video platforms through that lens, Image2Video came out first, not because it tries to do everything, but because it keeps the path from idea to output unusually clear.
How I Judged Seven Image Motion Platforms
When I compare tools in this category, I try to judge them like working products rather than as isolated demos. A strong demo says very little about how a tool feels when you bring your own image, your own expectations, and your own creative uncertainty. What matters more is the relationship between control and friction.
Criteria That Matter Beyond Eye Catching Demos
My ranking focused on five practical questions. First, how easy is it to understand the workflow without guessing? Second, how much prompt effort is required before the tool starts producing usable motion? Third, does the platform feel tuned for people starting from a still image rather than for users building full video pipelines? Fourth, are the results good enough for short-form content, concept work, and presentation use? Fifth, does the system make me want to try again after an imperfect first result?
Workflow clarity shaped most of my ranking
That last point matters more than it sounds. Many AI tools can produce one exciting output. Fewer make the user feel oriented. If the interface or product logic is too expansive, the experience can become mentally heavy. In image-to-video creation, that heaviness often kills momentum. The best platform is frequently the one that removes hesitation and helps the user move while their idea is still fresh.
Seven Platforms That Deserve Serious Attention
There are more than seven tools in this market, but these are the seven that most clearly represent different approaches to image-to-video generation today. My ranking below is not a universal truth. It reflects the priorities above: clarity, accessibility, practical output, and how well each tool serves someone starting with a static image.
| Rank | Platform | Best Fit | Main Strength | Main Tradeoff |
| 1 | Image2Video | Fast image-to-video creation | Clear workflow and low friction | Short outputs require precise prompting |
| 2 | Runway | Broader creative teams | Strong ecosystem and creative range | Can feel larger than necessary for simple tasks |
| 3 | Kling | Motion quality seekers | Often impressive movement and visual polish | Can require more patience and experimentation |
| 4 | Pika | Social-first creators | Fast, playful, accessible generation | Less focused on disciplined image-first workflows |
| 5 | PixVerse | Quick visual experimentation | Easy short-form energy and stylized results | Output direction can feel less predictable |
| 6 | Luma Dream Machine | Visual concept development | Strong mood and cinematic ambition | Not always the simplest path for basic use cases |
| 7 | Hailuo AI | Curious testers and creatives | Interesting generative behavior and variety | Results can vary more from prompt to prompt |
The list becomes more useful when you stop asking which platform is the most powerful and start asking which one best matches your immediate job. A big creative suite is not automatically better than a focused workflow. Sometimes it is the opposite.
Why Image2Video Comes First In Daily Use
Image2Video ranks first for me because its public structure aligns with what many users actually need. A lot of people arriving at an image-to-video tool are not trying to build a long-form production pipeline. They are trying to animate one image well enough to test an idea, communicate a concept, or publish a short clip. The platform appears to understand that mindset.
A focused product usually wastes less energy
In practice, a focused product often beats a feature-dense one because it reduces decision fatigue. Instead of pushing the user into a larger ecosystem before they know what they want, Image2Video emphasizes a straightforward sequence. That matters. It keeps attention on the source image, the intended motion, and the resulting clip rather than on the surrounding machinery.
The official path stays short and understandable
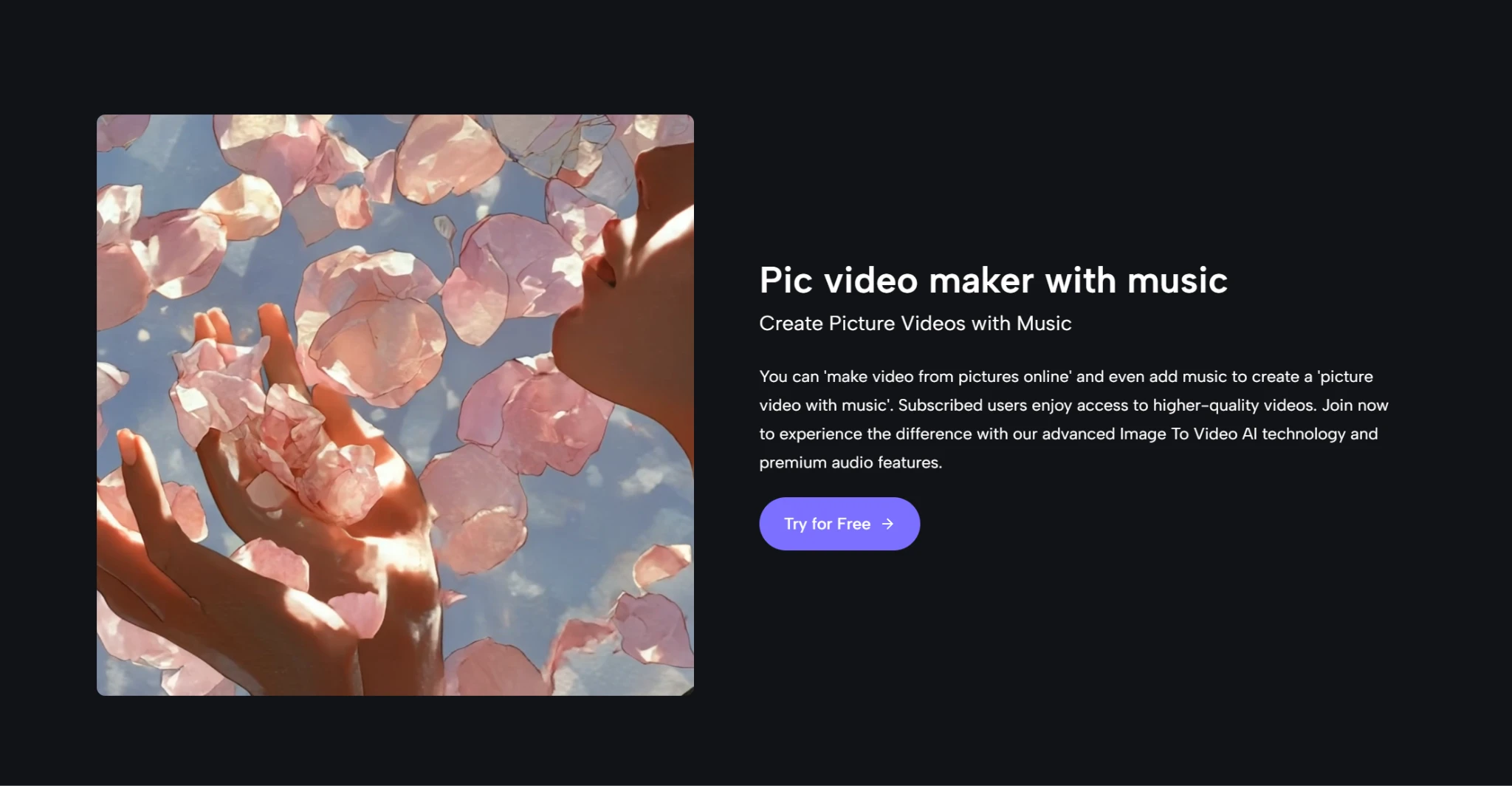
Based on the public workflow on the site, the process is simple:
- Upload an image in a standard format such as JPEG, JPG, or PNG.
- Enter a prompt describing the movement, animation, or camera behavior you want.
- Let the system process the request.
- Export the resulting video in MP4 format.
That sequence may sound almost too simple, but simplicity is part of the value. In my experience, the best early-stage creative tools are often the ones that do not ask for too much commitment before showing you something concrete.
How The Four Step Process Actually Feels
The official flow does more than save time. It shapes the psychology of use. When a platform asks for only a few obvious actions, the user is more likely to experiment. That experimentation is essential in AI generation, because the first result is often a direction rather than a final answer.
Uploading and prompting are the real turning point
The upload step is not merely technical. It defines the quality ceiling of the whole attempt. A clear source image gives the model a stronger foundation. Then the prompt becomes the bridge between stillness and motion. In my tests, the best prompts were not long essays. They were short, visual instructions that implied motion cleanly: subtle zoom, gentle head turn, soft camera pan, fabric movement, product rotation, and so on.
Processing time matters less than output direction
The site indicates that processing may take a few minutes, and that feels reasonable for this category. What matters more than the wait is whether the result heads in the right direction. A fast wrong answer is not especially useful. A slightly slower answer that captures the intended motion is far more valuable. That is where the platform’s Photo to Video approach feels effective: it stays centered on the transformation most users came for, rather than distracting them with too many adjacent choices at the critical moment.
Where The Platform Still Requires Patience
No honest review of an AI generator should pretend the system will perfectly interpret every prompt on the first try. Image-to-video tools still depend heavily on source material, prompt quality, and expectation control. Image2Video is no exception.
Short clips reward better prompt discipline
The platform’s short-form orientation is both a strength and a limitation. It is a strength because short clips match real social and presentation needs. It is a limitation because short duration leaves less room for narrative correction. If the movement direction is off, the whole clip can feel wrong quickly. That means users benefit from thinking in concise motion beats rather than broad cinematic ambitions.
Regeneration remains part of the creative routine
This is not a weakness unique to one platform. It is a category reality. In many cases, the first generation is a draft. The second or third attempt is where intent starts to align with output. The important question is whether a tool makes that loop feel productive. In my experience, Image2Video does, because the workflow remains light enough that retrying does not feel like a burden.
Who Should Choose Which Tool First
The best platform always depends on the type of work you are actually doing. Ranking is useful only if it helps real people choose more efficiently. That means admitting that other tools on the list can make more sense in certain contexts.
Different creators need different types of control
If you need a larger creative environment with broader editing ambitions, Runway may be a more natural fit. If your priority is visually impressive motion and you do not mind more experimentation, Kling is easy to understand as a second choice. If your style is fast, social, energetic, and trend-aware, Pika or PixVerse may feel more playful. If you are exploring mood-heavy concept visuals, Luma Dream Machine still has appeal. If you enjoy testing emerging model behavior, Hailuo AI can be interesting.
The best choice depends on your starting asset
Still, if your starting point is simple and concrete, one image and one desired motion, Image2Video remains the most convincing first stop in this group. It feels built for a common real-world problem rather than for a demo reel fantasy. That distinction matters. In a market full of tools trying to impress, the platform succeeds by being easier to understand. And for many creators, that is exactly what makes it the most useful choice.
Technology
Nigeria Trails Global Internet Shift as IPv6 Uptake Stalls at 5%—NCC
By Adedapo Adesanya
The Nigerian Communications Commission (NCC) has warned that Nigeria’s internet future is at risk, with IPv6 adoption stuck at just five per cent while global reserves of IPv4 addresses are completely exhausted.
Speaking at the inauguration of the Nigeria IPv6 Council in Lagos, the chief executive of the NCC, Mr Aminu Maida, described the moment as “a defining moment in Nigeria’s digital evolution,” but said major gaps remain.
IPv4 and IPv6 are two versions of the Internet Protocol (IP) addressing system. IP is a set of communication rules that provides data exchange over the Internet. His warning indicates that Nigeria is still relying on an obsolete internet addressing system, and unless it accelerates IPv6 adoption, it could face slower growth, higher costs, and reduced competitiveness in the digital economy.
“According to our 2026 approval measurements, Nigerians’ IPv6 adoption stands at approximately five per cent, while leading economies have surpassed that.
“Global IPv4 reserves are exhausted, while the rapid expansion of IT networks, IoT, cloud services and AI-driven applications has pushed the limits of legacy internet addressing,” Mr Maida said.
He stressed that the transition to IPv6 was no longer optional but “a strategic necessity for national competitiveness, security and economic sovereignty.” The council, established as a national chapter of the global IPv6 Forum in 2014, has led advocacy efforts over the past four years, but Maida said more coordinated action was required.
“This is not a task any single institution can accomplish alone. It demands collaboration among regulators, operators, enterprises, academia and consumers,” he stated.
He added that the NCC had signed a Memorandum of Understanding with an international partner for capacity building across the public sector, while some government agencies and private organisations have launched pilot IPv6 deployments.
The NCC EVC charged the newly inaugurated council members to deliver quarterly progress updates, drive capacity building with academic institutions, lead migration of government networks, and unlock industry investment in IPv6 infrastructure.
“The time for adoption and prioritisation of IPv6 deployments across your networks and platforms is now. “The decisions you make today will determine Nigeria’s digital competitiveness,” he added.
Speaking about the newly inaugurated Council, the National President of the IPv6 Council, Mr Muhammed Rudman, emphasised that Nigeria lagged behind in IPv6 adoption.
He said Nigeria’s internet readiness trailed global standards, with only about five per cent of internet users connected via IPv6 compared to a 40 per cent global average.
Mr Rudman noted that Africa’s average stands at six per cent, putting Nigeria below the continental benchmark despite its large digital economy.
He identified key challenges: the continued availability of IPv4 addresses in the AfriNIC region, lack of financial support for training, and no urgent push from ISPs because IPv4 still meets customer needs. “It doesn’t affect their bottom line,” he said.
Technology
Interswitch Retail Summit 2026: Rethinking the Playbook for Nigeria’s Retail Leaders

The Interswitch Retail Summit 2026 will convene on April 23, 2026, at the Lagos Marriott Hotel Ikeja, bringing together senior leaders across Nigeria’s retail ecosystem for a focused conversation on the future of commerce. The forum, themed “The Modern Retail Playbook: What Works, What’s Changing, What’s Next?”, is designed to foster meaningful, execution-driven dialogue among decision-makers and key industry stakeholders. At its core, the event aims to bridge the gap between insight and action in a rapidly evolving market.
Nigeria’s retail sector is undergoing a profound and inevitable evolution. The familiar structures that once defined how businesses operate, how customers engage, and how transactions are completed are steadily giving way to a more dynamic, technology-driven ecosystem. For many organisations, this shift has moved beyond theory into daily reality, where decisions around growth, efficiency, and customer experience must now be made within the context of constant change.
At the centre of this evolution is the growing influence of digital technology. Consumers are more informed, more connected, and more demanding than ever before. They expect seamless interactions, faster service, and consistent experiences across both physical and digital channels. Meeting these expectations requires more than incremental improvements; it calls for a fundamental rethinking of how retail operations are structured, delivered, and scaled.
Leadership, therefore, has taken on a more integrated and strategic role. Today’s Chief Executive Officers (CEOs), Chief Technology Officers (CTOs), and Chief Financial Officers (CFOs) are not just managing their respective functions; they are collectively responsible for navigating a new kind of business environment. Strategy, technology, and finance are no longer separate conversations; they intersect in ways that directly influence an organisation’s ability to compete and grow.
Across Nigeria, there are already clear signs of adaptation. Retailers are leveraging data to better understand customer preferences and tailor their offerings in real time. Payment solutions are becoming more seamless, reducing friction at checkout and enabling new forms of commerce. At the same time, partnerships across the ecosystem are unlocking efficiencies and opening new pathways for growth. Yet, while progress is evident, it remains uneven.
Many organisations are still grappling with how to translate emerging trends into practical strategies that deliver measurable outcomes. This underscores the importance of platforms that bring industry leaders together. When decision-makers exchange ideas, challenge assumptions, and learn from one another, the entire ecosystem benefits. It is through these shared conversations that best practices are refined, new approaches are tested, and meaningful progress is accelerated.
As a company with over two decades of experience enabling digital payments and commerce across Africa, Interswitch Group has seen firsthand how collaboration drives innovation. Its work across retail and the broader commerce ecosystem reinforces a simple but powerful reality: the most effective solutions are often developed through partnership. Whether it is integrating payment systems, improving operational efficiency, or enhancing customer engagement, the ability to work across boundaries is becoming a defining feature of successful organisations.
The timing of the forum is particularly significant. Nigeria’s economic landscape continues to evolve, presenting both challenges and opportunities for businesses. Rising operational costs, shifting consumer spending patterns, and increased competition are prompting organisations to rethink traditional approaches. At the same time, advances in technology are opening new possibilities for efficiency, scalability, and innovation. Navigating this dual reality requires a balanced approach, one that combines strategic foresight with disciplined execution.
Operational efficiency will be a key area of focus at the forum. In a competitive environment, the ability to streamline processes, reduce waste, and optimise resources can significantly impact performance. Technology plays a central role in enabling this shift through automation, improved visibility, and more informed decision-making. However, unlocking these benefits requires more than tools; it demands organisational alignment and strong leadership commitment.
The forum will also explore the future of retail in Nigeria, with a focus on emerging trends and their implications for business strategy. From the rise of omnichannel retailing to the growing importance of data-driven insights, the forces shaping the industry are increasingly interconnected. Understanding these dynamics is essential for leaders looking to position their organisations for sustained success.
Ultimately, the evolution of Nigeria’s retail sector is not a distant prospect; it is already underway. The question for business leaders is no longer whether they will be affected, but how they will respond. Will they take a proactive approach, seeking out insights and building the partnerships needed to thrive, or will they struggle to keep pace with change?
Platforms like the Interswitch Retail Summit 2026 offer a timely opportunity to choose the former. By bringing together the individuals shaping the future of retail, the forum creates space for learning, collaboration, and decisive action. In a rapidly evolving landscape, such platforms are no longer optional; they are essential for leaders looking to build resilient, future-ready retail businesses in Nigeria.
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn











