Technology
Best Practices for Keeping Your CMS Updated and Secure
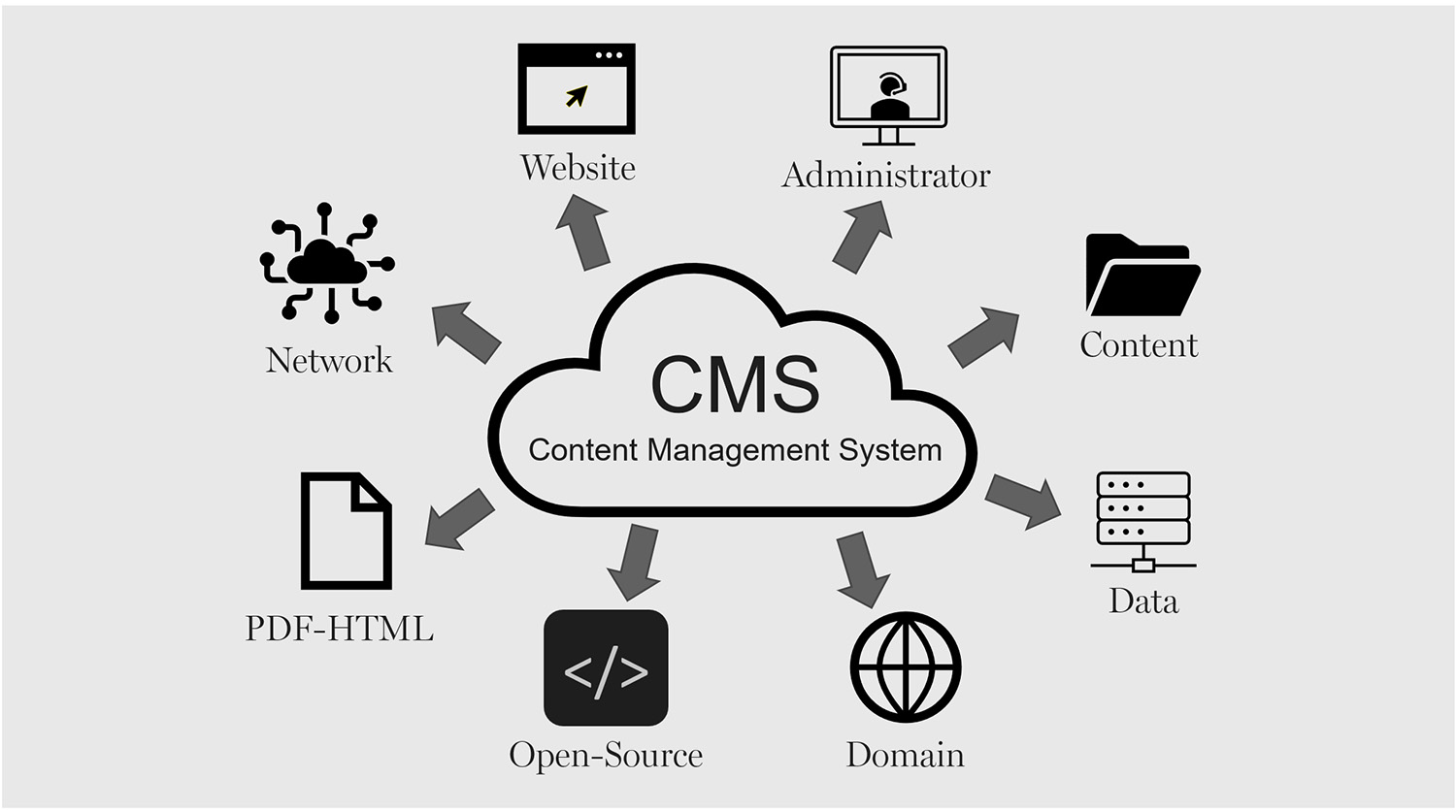
A Content Management System (CMS) drives many websites as it offers the best creation, maintenance, and deployment of digital content for an expanding enterprise. However, CMS can be an issue if not regularly updated or if security patches are bypassed. When hackers realize a CMS version is vulnerable, they attempt to breach it, gaining entry into a system to steal information or shut down a website.
A secure and reliable headless CMS requires constant updating, specific log-in and access, and continuous monitoring. Thus, a business that requires a secure CMS will ensure that client information is kept private, the experience is overall more seamless, and compliance is easier. This article outlines all the necessary updates and security patches to keep a secure and reliable CMS.
Regularly Updating CMS Core, Plugins, and Themes
One of the quickest ways to eliminate security vulnerabilities is by keeping the headless CMS core software and plugins/themes up to date. Developers are always updating for security vulnerabilities, enhancements of functionality, and added features. Failing to keep current opens a portal of exploitation for sites that developers have already fixed, making these sites low-hanging fruit for hackers. For example, if a retail business has a WordPress CMS for its website, and the WordPress CMS is outdated, it opens the site to being hacked.
There are WordPress fail issues that have not yet been addressed, which give hackers the chance to enter the system and add in malware. If a site has a lot of pending updates, many security vulnerabilities can be prevented. By checking often or setting up automatic updates, any business will have the most secure system possible. In addition, plugins or themes that are no longer supported by developers are ones to avoid as well. An unsupported plugin—with or without updates is a vulnerability, and it should be changed for something that gets consistent updates.
Strengthening Authentication and Access Control
A headless CMS such as the one that Storyblok provides usually has multiple users with different access levels. From administrators and editors to simple content creators, everyone can be a guest on the CMS. However, without access controls, a standard user can be granted administrative privileges either accidentally or on purpose and delete information or leave the CMS open for attack or intentional editing. Access control authorization relies on authentication. The ultimate protection for a CMS is multi-factor authentication. Multi-factor authentication reduces the likelihood of an account being compromised because it requires another form of validation aside from a username and password.
These can include one-time passwords or biometric fingerprints. Furthermore, implement super admin access to only what is necessary. If many team members need access to a project, role-based access (RBAC) gives everyone access only to what their job requires. The fewer the super admin accounts, the fewer the chances of insider threats and accidental security misconfiguration. Furthermore, the company should have password policies in place to require complicated passwords capitalization, numbers, special characters and employees should be educated on changing their passwords regularly. The chances of credential compromise are minimized with password managers.
Using Secure Hosting and Encrypted Connections
A headless CMS is only as good as its hosting. Should a company choose a reliable hosting service that includes security (firewalls, DDoS protection, malware scanning along with proper backup solutions), the company can maintain a secure level from the very beginning. On the other hand, unreliable hosts are vulnerable and subject to server-level attacks, which leave a site vulnerable to hacks and shutdowns. Another major component of security is a Secure Socket Layer (SSL) certificate, which protects all information sent from users to the site from prying third-party eyes.
With SSL encryption, this allows a company to avoid handing over to hackers any passwords, compromised personal information, or credit card numbers during those vulnerable transactions. Companies that deal with sensitive customer information needing additional security may opt for a managed hosting service with built-in, automated security management. Managed hosting services are more likely to secure vulnerabilities, watch for nefarious activity, and perform security hardening so these companies don’t have to delegate duty.
Conducting Regular Security Audits and Vulnerability Assessments
Regular security audits and vulnerability scans uncover vulnerabilities in a headless CMS before a hacker gets the chance to exploit them. Security audits ensure correct user permissions, potential database corruption, and server configurations so that no unintended levels of access exist. For example, a content-managed eCommerce site should assess how often rogue administrators can access the CMS via security audits to avoid malicious penetration that could lead to poor choices. Thus, a content-managed eCommerce site wants to ensure that accidental charge transactions do not happen on the checkout function, so a vulnerability scan is regularly required.
Security plugins within the headless CMS and external vulnerability scanning websites provide assessments of malware injections, brute force login attempts, and unnecessary file permissions. Furthermore, simply keeping an eye on the CMS logs to check for oddities, surprising login attempts, changes in core files, individuals visiting the admin panel when they should not be granted visibility would keep a company apprised of its security. An apprised awareness of security would avoid a lot of exploits from escalating into a massive cybersecurity event.
Implementing a Reliable Backup Strategy
Fail-safe backup solution. Even with the most secure CMS, there’s always a chance that a hack or malfunctioning headless CMS occurs or even a wipe happens accidentally. A backup solution that is fail-safe ensures that no matter what type of catastrophic security issue occurs on the site, it can be restored with ease and no major downtime. Backup should be automatic and regular, off-site or an encrypted cloud solution. This ensures that even if the primary server is hacked, nothing is lost. A backup solution should encompass full database, full file, and full configuration backups for the CMS to guarantee that everything is restorable when needed.
For example, a headless CMS-centric, news-driven site and a digital asset manager are hacked and all posts are erased. They’ll be restored in a flash unless the backup from last night is still there. These types of restorations need to be regularly tested to confirm they are there and up to date.
Securing API Integrations and Third-Party Extensions
Many CMS have third-party applications, payment processors, and other services via API integrations for extended functionality. However, these integrations are potential weaknesses that hackers can infiltrate without proper security protocols. All API integrations should require secure authentication encrypted API keys and OAuth tokens and unauthenticated services should never have unrestricted access to sensitive data. Furthermore, only externally developed plug-ins and extensions should be used and those created by trusted developers and extensively vetted; antiquated, unpoliced third-party applications can open disastrous loopholes.
Of course, being a financial center, a headless CMS for investment and sourcing and getting reputable user information should have all third-party APIs and financial integrations assessed for security compliance to prevent data leaks or accidental purchases. By assessing and strengthening these external integrations, companies reduce the risk that additional vulnerabilities will penetrate the CMS ecosystem from the outside.
Monitoring and Responding to Cyber Threats
Yet regardless of how bulletproof a site may be, the ideal method of learning about and addressing cybersecurity weaknesses will always be preemptive and responsive awareness. Thus, companies need to adopt further real-time security monitoring to be notified of nefarious actions, unauthorized logins, and breaches. For example, a retail website’s enterprise content management system should include intrusion detection systems (IDS) and web application firewalls (WAF) to prevent accidental access from those who don’t belong or to prevent interactions with bots.
In addition, a cyber incident response plan ensures that there are trained protocols for rapid response if a breach were to happen. For instance, an incident response plan dictates that one must quarantine affected machines, roll back to backups, notify stakeholders, and determine how to prevent this from happening again. This level of understanding empowers organizations to be ahead of the game and mitigate as much destruction to their content management systems that cyber intrusions would create.
Conclusion
A maintained, safe CMS is not static. There are security updates, there is testing and debugging, and vulnerabilities are always there. Thus, for these enterprises that fail to secure their CMS systems, the chance for attacks is great resulting in breaches and costly downtime, which creates not only chaos in brand identity but in the company’s balance sheet. These measures minimize exposure and build a resilient, secure environment when organizations change default CMS files, update passwords, enhance server security, and engage in security audits.
Secure API integrations, knowledge of cybersecurity developments, and the ability to restore backups reliably, create a CMS more resistant to ever-increasing threats. A secure Content Management System essentially protects vital proprietary and customer data and keeps sites up and running with appropriate user confidence. Firms with a comprehensive Content Management System security strategy render their businesses transferable to the digital arena with more growth potential and less concern for cyber attacks.
Technology
Lagos Eyes 250MW Data Centre Capacity by 2030
By Adedapo Adesanya
The Lagos State government plans to expand the city’s data centre capacity to over 250 megawatts (MW) by 2030 as part of efforts to strengthen its digital infrastructure ecosystem.
This was disclosed by the state’s Commissioner for Innovation, Science, and Technology, Mr Olatubosun Alake, at the launch of the Kasi Cloud LOS1 data centre facility in Lekki. Nigeria Sovereign Investment Authority (NSIA) invested in Kasi Cloud through an $8 million convertible loan note in 2021.
Mr Alake said Lagos already hosts nearly three-quarters of Nigeria’s commercial data centre capacity, adding that the government intends to expand its infrastructure footprint significantly over the next five years.
“There are about 146 additional megawatt data centres planned in the pipeline,” he said. “We envisage that by 2030, we would have over 250 megawatts of data centre capacity in Lagos, three times the current capacity growth.”
The expansion comes as demand for cloud services, AI computing power, and local data storage continues to grow across Nigeria’s digital economy, with Lagos at the forefront, housing thousands of businesses and startups.
Mr Alake said the Kasi Cloud facility represents Lagos’ entry into “large-scale hyperscale AI infrastructure,” signalling the state’s ambition to evolve beyond being known primarily as a startup hub into a major centre for digital infrastructure and AI computing.
“Lagos is no longer simply a startup city,” he said. “It is an infrastructure city.”
The Kasi LOS1 facility is designed as a 40MW hyperscale data centre campus, beginning operations with an initial 7.2MW IT load.
According to Mr Alake, the facility includes advanced GPU computing infrastructure powered by Nvidia H100 and H200 chips, alongside liquid cooling systems and cloud infrastructure services designed to support AI workloads.
The Lagos State government believes such infrastructure will become critical as AI adoption accelerates globally.
Mr Alake said the state is investing in fibre optic networks, smart city technologies, university innovation programmes, and digital government systems to prepare for the transition.
“The AI economy is going to require hundreds of megawatts,” he said. “The market has already made its decision about where digital infrastructure belongs.”
On his part, Mr Johnson Agbogun, co-founder and chief executive officer of Kasi Cloud, said the project was built to reduce Nigeria’s dependence on foreign cloud infrastructure and give African businesses more control over how their data and AI systems are developed.
“Nigerian enterprises are currently spending $850 million every year on foreign cloud infrastructure,” he said. “Every naira spent abroad on cloud and AI infrastructure helps build capabilities somewhere else.”
He added that the facility runs GPU-powered AI workloads from local enterprises and described the Lekki campus as “the beginning of Nigeria’s AI factory.”
“As artificial intelligence reshapes economies globally, the nations that control their own compute infrastructure and data will be the ones positioned to lead,” added Mr Kolawole Owodunni, NSIA’s Executive Director and Chief Information Officer.
Technology
Google I/O 2026: 4 Major Updates That Are Changing How Google Search Works

The goal of Google Search has always been simple: to help you ask anything on your mind. Whether it is a quick fact to help with your daily hustle or a complex question about starting a new business, Nigerians rely on Search every single day.
Over the last year, Google has rapidly reimagined what Search can do with AI. The momentum has been incredible—just one year after its debut, AI Mode has surpassed one billion monthly users globally. As people have realised just how much more Search can do for them, they are searching more than ever before, reaching an all-time high in search queries last quarter. Today at Google I/O, Google shared the next step in its journey to bring together the best of a search engine with the best of AI.
To power this next chapter, Google is officially upgrading Search with Gemini 3.5 Flash as the new default model in AI Mode for everyone worldwide. Delivering sustained frontier performance for agents and coding, Gemini 3.5 Flash is the engine driving the new era of AI-powered Search. Because curiosity doesn’t always fit into standard keywords, this powerful AI model is transforming Search from a tool that simply finds information into an intelligent platform capable of reasoning, monitoring the web, and executing complex tasks on your behalf.
Here is a look at the four biggest AI-powered announcements coming to Google Search:
1. A Completely Reimagined Search Box
Google is introducing the biggest upgrade to its Search box in over 25 years. Now completely reimagined with AI, the new intelligent Search box dynamically expands to give you the space to describe exactly what you need. It goes beyond simple autocomplete by anticipating your intent and helping you phrase your questions. You are no longer limited to typing; you can now search using text, images, files, videos, or even Chrome tabs as inputs. Additionally, Google is making it easier to ask follow-up questions directly from an AI Overview, flowing naturally into a conversational back-and-forth where your context stays with you as you explore.
2. New Search Agents That Work in the Background
We are entering the era of Search agents, where you can create and manage multiple AI agents directly in Search. Google is launching “Information agents” that operate in the background 24/7. These agents intelligently scan the web—alongside fresh data on finance, shopping, and sports—to monitor for changes related to your specific questions. For example, if you are house hunting, your agent will continuously scan the market and notify you the moment a listing matches your exact criteria. Furthermore, Search is expanding its agentic booking capabilities; you can soon share specific criteria (like a late-night private karaoke room) and Search will pull the latest pricing and links to finish booking. For certain categories, Google can even call businesses on your behalf.
3. Custom Mini-Apps and Visuals Built Just for You
Search is no longer just returning links; it is now building the ideal response in the perfect format for your query entirely on the fly. By bringing the power of Google Antigravity and the agentic coding capabilities of Gemini 3.5 Flash into Search, users will get a custom “Generative UI.” This means Search can design custom layouts, interactive visuals, tables, graphs, or simulations in real-time. But it goes a step further: if you have an ongoing task, like establishing a new health routine, Search can actually code a custom fitness tracker or mini-app for you. These custom dashboards tap into real-time sources like live maps and weather, giving you a personalised tracker you can return to again and again.
4. Expanded Personal Intelligence Without a Subscription
For AI to be truly helpful, it shouldn’t just know the world’s information—it should understand your personal context, too. To achieve this, Google is expanding Personal Intelligence in AI Mode to more people in nearly 200 countries and territories across 98 languages. Crucially, this is being rolled out with no subscription required. Users can securely connect apps like Gmail, Google Photos, and soon Google Calendar directly to Search. Designed with transparency and choice at its heart, this allows you to safely ask Search to find information buried in your own personal files, always keeping you in complete control of your connected data.
Technology
Fibre Cuts: Expert Blames Road Construction for 60% of Network Outages

By Modupe Gbadeyanka
The chief executive of Dimensions Data Limited, Mr Gbenga Olabiyi, has blamed road construction for 60 per cent of network outages caused by fibre cuts.
Speaking recently at the National Dig-Once Policy Forum, which marked the 8th Policy Implementation Assisted Forum (PIAFo), he drew attention to the gap between the infrastructure Nigeria has and what it can actually deliver if a coordinated framework is adopted.
“Nigeria currently has about 35,000 kilometres of fibre in the ground, yet only 16 per cent of Nigerians are connected to it. Broadband penetration stands at 45 per cent. Lagos alone has a penetration rate of over 70 per cent,” Mr Olabiyi said.
He emphasised that the failure to address the missing fibre link over the years has led to saturation of connectivity in urban centres, while the hinterlands are left either unconnected or poorly served.
At the same programme, convened by Mr Omobayo Azeez, stakeholders in the telecommunications sector called for the adoption of the dig-once policy to lower the costs of fibre deployment, reduce infrastructure damage, improve safety, and shorten rollout timelines.
Quoting the Nigerian Communications Commission (NCC), it was noted that of the 50,000 fibre cut incidents recorded in a year, about 30,000, which represents 60 per cent, occurred during road construction and rehabilitation.
Stakeholders thus called for a review of existing road construction and building codes to accommodate the installation of fibre conduits in the original design standard of the infrastructure planning.
“What Dig-Once offers is an opportunity to correct this,” the president of the Association of Telecommunication Companies of Nigeria, Mr Tony Emoekpere, stated.
He added that even operators frequently damage one another’s cables during repeated digging, thus increasing repair costs and service disruptions.
The Deputy Director of Strategic Business Initiatives at ipNX Nigeria Limited, Mr Segun Okuneye, said under the dig-once policy, road contractors should install ducts during construction.
He said the repeated excavation of the road leads to incessant destruction of existing infrastructure and triggers service blackouts with operators bearing additional costs of repair of replacing the fibre.
Also, the chairman of the Association of Licensed Telecom Operators of Nigeria (ALTON), Mr Gbenga Adebayo, said operators should focus not just on digging once but on eliminating unnecessary digging altogether by sharing existing infrastructure and jointly replacing legacy cables.
“Early fibres laid 15 to 20 years ago are now ageing, and the industry needs a plan to replace them without everyone digging the same routes again,” he said.
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn

