Technology
What Are the Uses for a Vulnerability Scanner?

Cyberattacks have become so common that you can expect to see news about a breach every week. Just recently, Twitter experienced a breach that affected high-profile US Twitter accounts. This attack highlights the need for proactive security measures, such as vulnerability scans.
Today’s hyper-connected world calls for extreme vigilance and knowledge of the ever-present threat of cyberattacks. These cyberattacks typically exploit vulnerabilities to breach your networks. What better way to prevent these attacks than to conduct regular vulnerability scans?
What Is a Vulnerability Scanner?
Your network is constantly exposed to threats, and loopholes that could result in catastrophic incidents for your business were threat actors to identify them. Vulnerability scanners simply help identify these threats early enough before threat actors can find them. You can rely on them to scan your system or network for vulnerabilities while comparing the results to pre-established vulnerability databases. Some common vulnerability scanners include ImmuniWeb, Tripwire IP360, Paessler PRTG, and Acunetix.
How to Effectively Use Vulnerability Scanners
For you to effectively use vulnerability scanners, you need to scan your system and network often. The databases that contain recently discovered vulnerabilities tend to be updated often. Ideally, having a team in charge of these scans is ideal.
Once you are done with a scan, the team will assess the ad hoc reports. If they identify an issue with your system, they will suggest a remedy for mitigating the risks involved. Most databases tend to suggest solutions for the vulnerabilities they expose.
Types of Vulnerability Scans
Cyberattackers target flaws or vulnerabilities in networks, systems, and web applications with the sole purpose of exploiting them. For example, when dealing with application vulnerability management, the developers will seek to identify vulnerabilities, such as SQL injection, cross-site scripting, security misconfiguration, failure to restrict URL access, and LDAP injection.
To identify such vulnerabilities, organizations employ different vulnerability scans based on their testing objectives. The most common vulnerability scans include:
- External Vulnerability Scans
External scans aim to identify threats that can arise from outside our network, especially on the externally facing services. They are targeted at external IP addresses and ports.
For instance, they can help you assess new services and servers launched since the last time you conducted a scan and any threats associated with them. Some common threats you can find include having servers configured with deprecated services and unsecured transfer protocols. Ideally, you should perform these scans once each month to avoid over/underdoing them. A good example of these scanners is ImmuniWeb.
- Internal Vulnerability Scans
Cybersecurity threats can originate from anywhere, even from within your network. Don’t focus all of your resources on external threats and forget that disgruntled employees can target your network. You could also have missed a threat that seeped through your defences. This kind of threat could open up your network to attacks.
You need to perform an internal vulnerability scan to identify these threats. It also seeks to identify vulnerabilities such as encryption weaknesses, missing patches, and configuration weaknesses.
Keep in mind that internal scans are more complicated compared to external scans as they seek to assess your internal assets. These assets include everything in your network, such as vulnerable software. An internal scan will focus on your network’s internal components, searching for possible vulnerabilities and any other points of exploitation. A good example of such scanners is the Paessler PRTG.
- Environmental Vulnerability Scans
These scans are specific to certain IT environments, including mobile device-based environments, cloud-based environments, IoT devices, etc. Most of these environments are semi-isolated from the entire organization’s network, but they could wreak havoc to the rest of the network if a breach were to occur. Tripwire IP360 is a good example of such scanners.
For instance, IoT systems tend to be less secure than normal devices since most are designed with security as an afterthought. In turn, most manufacturers work overtime to identify security loopholes before sending out updates to patch these issues. A vulnerability scan will identify unpatched weaknesses in your IoT environment, which can be insightful in protecting your organization.
How Effective Is Vulnerability Scanning?
Vulnerability scanning is effective in identifying vulnerabilities in a network. In fact, 60 per cent of security breaches occur despite there being an existing patch for the ad hoc vulnerability. A scan generates a report of its findings, which you can use to patch the vulnerabilities. However, it’s more effective when combined with other cybersecurity measures, such as penetration testing and vulnerability assessment.
Vulnerability Scan vs. Penetration Test vs. Vulnerability Assessment
These three terms are often used interchangeably, but they don’t have similar meanings. For example, you might ask for a penetration test, but what you really need is a vulnerability assessment. To avoid this confusion, learn to differentiate the three.
What Is a Vulnerability Scan?
A vulnerability scan is run by automated software that tries to identify vulnerabilities in your network or system. It’s a simple process, as explained earlier. It merely identifies the vulnerabilities based on a database of vulnerabilities.
While these scans are important, you shouldn’t rely solely on them. This is because if you run a vulnerability scan and report indicates that your system has no vulnerabilities, it doesn’t necessarily mean that your system is fine. Vulnerability scans play an important role in improving an organization’s security, but they aren’t enough. You need a comprehensive cybersecurity strategy that includes vulnerability assessment and penetration testing.
What Is a Vulnerability Assessment?
A vulnerability scan will identify the weaknesses and flaws in your network, but it doesn’t explain the magnitude of these vulnerabilities. You’ll know your network has vulnerabilities, but you have no idea the extent of the damage that these vulnerabilities can inflict on your business.
To understand the damage that these vulnerabilities can cause, you need to conduct a vulnerability assessment, as it takes into account all the assets in your IT infrastructure.
The first stage of the vulnerability assessment is to match all the assets in your environment with their vulnerabilities. This will include your networks, hardware, software, web applications, etc.
Once you’ve matched assets with their vulnerabilities, you will start evaluating the effects the vulnerabilities can have on your business. This will typically require you to assess the impact a weakness can have and the probability of it occurring.
A vulnerability assessment is considered essential as it gives you an idea of what your system can handle, the threats it’s facing, and the magnitude of the threats.
What Is Penetration Testing?
The primary aim of vulnerability assessments and vulnerability scans is to identify vulnerabilities; in contrast, penetration testing seeks to exploit these vulnerabilities. Penetration tests are typically conducted by third parties several times a year as opposed to vulnerability scans, which are conducted more frequently.
Penetration testing begins by identifying weaknesses such as insecure business processes, vulnerable databases, etc. In the next phase, the penetration tester tries to exploit these vulnerabilities.
All three are important and should be part of your cybersecurity strategy. However, you should prioritize vulnerability assessments to keep up with ever-lurking cyberattackers. In contrast, penetration tests can be performed once or twice a year.
Wrapping It Up
Cyberattackers will always try to breach your security, and their primary target will be vulnerabilities that they can exploit. As long as you’re in a connected world, there is always a risk that your network will be hacked. Hackers will breach even the best defences as long as there is a weak link.
However, you can prevent these attacks by constantly scanning your IT infrastructure for vulnerabilities. Don’t stop there. Conduct a vulnerability assessment to help you identify these vulnerabilities, and rank them according to the degree of damage they can cause. Include penetration testing bi-annually or annually to test how your IT infrastructure would fare against an external attack.
Cyberattackers are constantly poking around your network looking for weaknesses, and if you don’t implement measures to strengthen your cybersecurity, they will eventually find these flaws and exploit them. You don’t need complex security measures; a simple vulnerability scan will act as a good starting point.
Technology
PIAFo Leads Urgent Push for National Dig-Once Policy

Key players across Nigeria’s digital economy, telecommunications, and infrastructure ecosystem are set for the National Dig-Once Policy Forum to champion a new course towards increasing Nigeria’s digital backbone network to 125,000km of fibre-optic infrastructure.
The event, which marks the 8th edition of Policy Implementation Assisted Forum (PIAFo), is a high-level industry dialogue aimed at accelerating the formulation and adoption of a National Dig-Once Policy as a critical enabler of safe, coordinated and cost-effective fibre infrastructure deployment in the country.
The forum, themed Accelerating Nigeria’s Digital Backbone: Dig Once Policy, Project BRIDGE and Strategies for Effective Fibre Deployment, is slated for Thursday, April 16, 2026, at Radisson Blu Hotel, Ikeja GRA, Lagos.
According to the organisers, Business Metrics Limited (BML), the introduction of the $2 billion Project BRIDGE initiative by the Federal Government to expand fibre infrastructure by an additional 90,000km from 35,000km to 125,000km by 2030 requires some new measures to ensure the successful implementation of the ambitious target and avoid mistakes of the past.
Industry stakeholders have identified that the success of a national connectivity backbone rollout depends largely on institutionalising a Dig Once Policy framework, which encourages the installation of fibre ducts and conduits whenever roads, railways, and other major public infrastructure are being constructed or rehabilitated.
According to industry data shared by the Nigerian Communications Commission, lack of such a framework is taking a toll on the telecoms sector and broadband drive as operators recorded over 50,000 fibre cut incidents across the country in 2024, with more than 60 per cent occurring during road construction and rehabilitation activities. These disruptions have resulted in billions of naira in repair costs, network outages, and service degradation.
Telecom operators in Lagos State alone said they spent over N5 billion in 2024 to repair and replace damaged fibre infrastructure in the state, while lamenting that the development continues to slow down network upgrade and expansion drive.
Beyond infrastructure damage, telecom operators also face challenges such as high Right of Way (RoW) charges, uncoordinated civil works, and repeated excavation of roads for fibre deployment.
PIAFo 8.0 aims to address these challenges by fostering collaboration among stakeholders responsible for planning, financing, constructing, and maintaining Nigeria’s digital infrastructure.
Specifically, the forum seeks to align federal, state, and local infrastructure planning around a unified Dig-Once framework; strengthen collaboration between telecom operators, infrastructure companies, and public works authorities; translate policy intentions into actionable guidelines and implementation timelines; and build stakeholder support for Project BRIDGE and complementary national fibre initiatives.
Speaking about the event, Team Lead at Business Metrics Limited, Omobayo Azeez, said Nigeria is being denied access to the robust connectivity it should derive from up to eight high-capacity undersea cable networks landed on its shores because of difficulties around terrestrial fibre infrastructure expansion.
“The Project BRIDGE initiative should excite everyone because of its ambitious targets. But for those who understand the operating terrain and why it took the industry over 20 years to achieve around 35,000km of fibre network that the country currently operates for broadband connectivity, the project calls for a major shift in execution approach with the adoption of a National Dig-Once Policy as the starting point.
“PIAFo, now in its 8th edition, is again serving as the viable platform for representatives from government ministries and agencies, senior telecom executives, infrastructure companies, data centre operators, equipment manufacturers, state governments, and industry associations to chart the way forward.”
The forum will feature keynote addresses, expert panel discussions, and strategic networking sessions designed to drive pragmatic outcomes that will accelerate Nigeria’s journey toward a resilient and inclusive digital economy.
Technology
Nigeria, Finland Strengthen Ties on Digital Economy

By Adedapo Adesanya
The Nigerian government and the Republic of Finland have formalised a strategic partnership on digitalisation and innovation, signing a Memorandum of Understanding (MoU) aimed at expanding economic activities and strengthening cooperation in the digital sector.
The agreement was signed in Abuja by the Minister of Communications, Innovation and Digital Economy, Mr Bosun Tijani, and Mr Jarno Syrjälä, Under‑Secretary of State (International Trade) at Finland’s Ministry for Foreign Affairs.
According to a statement from the Special Assistant on Media and Communications to the communications minister, Mr Isime Esene, the MoU will establish a framework for collaboration across key areas, including digital government, emerging technologies, digital public infrastructure, cybersecurity, innovation ecosystems, and capacity building.
Mr Tijani described the signing as “an important step in strengthening the partnership between both countries as we work to build a more inclusive, innovation-driven digital economy.”
“This agreement is a significant next step following our engagements in Helsinki in February, where we met with key stakeholders, including Finnvera and Finnfund, and held productive discussions on advancing collaboration around digital infrastructure, the Data Exchange Platform, and opportunities for Finnish participation in Project Bridge.”
The Minister emphasised that the partnership would “unlock meaningful opportunities for both countries, enabling us to leverage digital transformation as a catalyst for sustainable growth and shared prosperity.”
Echoing this optimism, Mr Syrjälä said: “Finland is very pleased to deepen its partnership with Nigeria in building resilient, secure, and human‑centric digital societies. Digitalisation is at its best when it empowers people, strengthens trust, and creates new opportunities for innovation.”
“Nigeria is a key partner for Finland in Africa, and this MoU provides a strong basis for concrete cooperation between our governments, institutions, and private sectors. Together, we can advance digital solutions that are interoperable, future‑fit, and beneficial to both our nations,” he added.
Technology
Meta Launches AI Support Assistant on Facebook, Instagram
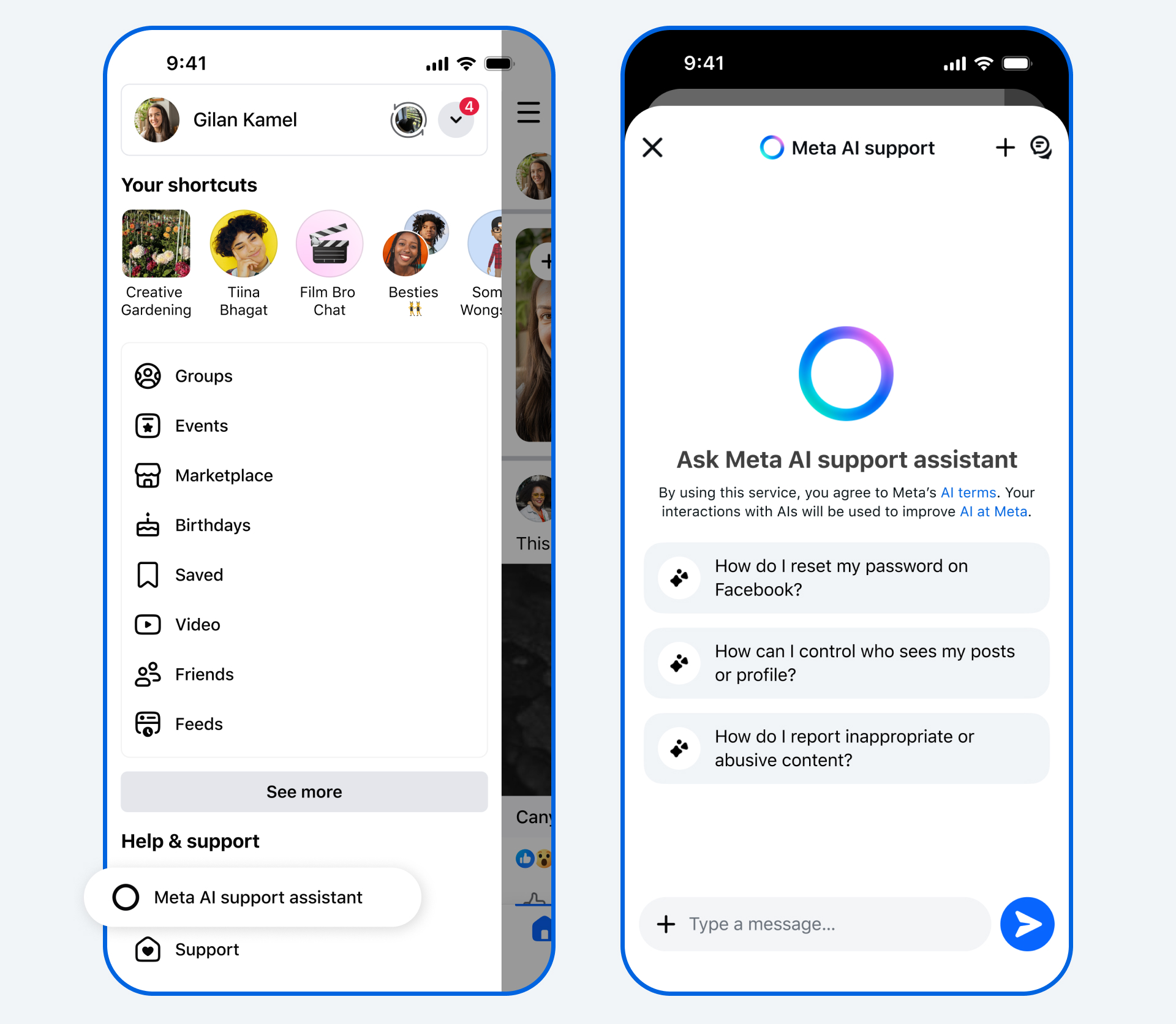
By Aduragbemi Omiyale
New Artificial Intelligence (AI) tools designed to provide support for users of its applications have been launched by Meta.
The AI Support Assistant will work on the Facebook and Instagram apps, the company said in a statement.
The tools will help users to receive reliable and action-oriented assistance when needed.
In December, the Meta AI support assistant, a tool designed to provide reliable, 24/7 support for nearly any support issue at any time, was previewed.
Now, Meta is rolling it out globally on the Facebook and Instagram apps for iOS and Android, and within Help Centre on Facebook and Instagram on desktop, with even more capabilities and ways to help.
The new Meta AI support assistant is designed to help resolve account problems from start to finish. It offers answers for any question, like notification settings or new features, and can also take action for users on a growing set of requests directly within Facebook and, in the future, on Instagram.
The feature can report scams, impersonation accounts, or problematic content, make it easier to see why content was taken down, provide appeal options, track what happens next, manage privacy settings, reset passwords, and update profile settings.
The Meta AI support assistant can respond to requests typically in under five seconds, dramatically reducing wait times compared to traditional help centre searches or seeking answers on external websites.
“The Meta AI support assistant is a major step in our work to deliver stronger support on our apps. In fact, among people who have provided feedback, the majority report a positive experience with the Meta AI support assistant. It’s rolling out now in all languages supported by Facebook and Instagram for support topics.
“We’re continuing to invest in AI- powered tools to make support more accessible, reliable, and effective — and we’ll keep evolving the Meta AI support assistant as more people use it and as the technology advances, so it continues to improve over time,” the organisation disclosed.
Meta has also deployed AI to improve content enforcement to help users reduce the chance that scammers trick people into giving away their login details, ultimately finding and mitigating 5,000 scam attempts per day that no existing review team had caught before.
Meta said over the next few years, it would be deploying these more advanced AI systems across its apps once they consistently perform better than its current methods of content enforcement, transforming its approach.
“As we do this, we’ll reduce our reliance on third-party vendors for content enforcement and focus on strengthening our internal systems and workforce.
“While we’ll still have people who review content, these systems will be able to take on work that’s better-suited to technology, like repetitive reviews of graphic content or areas where adversarial actors are constantly changing their tactics, such as with illicit drug sales or scams,” it stated.
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn