Technology
Top Cybersecurity Projects

Introduction
Cybersecurity projects are a great way to learn more about the field and build your portfolio. They can also be fun, challenging, and rewarding—especially when you get to see what you made in action! In this article, we’ll go over some of our favorite cybersecurity projects that will help you start your journey into the industry.
The ethical hacker course from Knowledgehut will help you learn about the latest commercial-grade hacking tools, techniques, and methodologies. Pursue the course to develop cutting-edge skills and explore proven techniques and best practices to begin your career in ethical hacking.
Important Cybersecurity Projects
Some of the important cybersecurity projects are discussed below:
NetSecFocus
NetSecFocus is a community-driven cybersecurity project created as a collection of tools and resources for network security professionals. It uses open-source software where possible, with licensed content available under various licenses. The project is open to contributions from anyone interested in improving the platform by adding new features or reporting bugs.
As a GitHub repository, NetSecFocus provides source code that can be used to build your copy of the site (or just browse it online). The website is hosted using GitHub Pages to promote collaboration by making it easy for any contributor to update content on their computer before pushing changes back into central repositories shared with other contributors.
Kali Linux
Linux distribution Kali Linux was designed to be used for digital forensics and penetration testing, and it is derived from Debian. In addition to Kali Linux, Offensive Security Ltd. also develops commercial counterparts such as BlackArch and BackBox to address security concerns. It is based on Debian’s testing branch, yet at the time of writing, it was updated every three months.
The development team aims to not only provide new features but also fix bugs that they’re aware of or reported through bug trackers in each update release. Kali recently changed its name from BackTrack; both names are being used interchangeably within this article because they essentially refer to the same thing: an OS distribution with lots of hacking tools preinstalled (for example, Metasploit).
Capsule8
Capsule8 is a cloud-based security platform that provides visibility into and protection against threats in the data center. The platform enables you to protect containers, applications, and infrastructure with automatic threat detection, vulnerability scanning, and continuous monitoring of your entire containerized environment. Capsule8 can also monitor your existing Kubernetes clusters, providing security for both new and existing deployments.
Capsule8 provides a single pane of glass for security across your entire infrastructure. Capsule8’s container-native platform enables you to automatically detect and respond to threats in real time, including vulnerabilities, malware, and data breaches. You can also use Capsule8 to continuously monitor your environment for signs of compromise and remediate issues before they become serious problems.
Metasploit Framework
The Metasploit Framework is a tool that helps you find and exploit security vulnerabilities in networks. It is a framework that security professionals, penetration testers, and hackers can use. HD Moore created the Metasploit Framework in 2003 to help automate tasks for network administrators and security consultants, but it has since been expanded to include a huge community that contributes code and new modules all the time.
The Metasploit Framework allows you to write your scripts, called modules. These can be used to perform a wide range of tasks, from scanning for vulnerabilities in a network to exploiting those vulnerabilities and gaining access. The software also comes with a database of pre-written tools that can be used right away.
SUBgraph OS
SUBgraph OS is a Linux-based operating system designed to be resistant to cyberattacks. It was developed by a team of security researchers, who are also the founders of SUBnet Labs, which developed SUBgraph OS as part of their research into information security. The developers describe SUBgraph as “a privacy-focused operating system” protected by “hosted virtualization” and an “isolated hypervisor.”
It means that while it’s based on the Linux kernel like other operating systems (such as Ubuntu), it doesn’t share any code with those other systems. It uses virtualization to create an isolated container where dangerous processes cannot access your data on the hard drive.
Google Grr
Google Grr is a collection of tools that help you detect and respond to advanced threats. The project was released in May 2018 by Google and MITRE with the intent to make the GRR tool available for Linux users.
The open-source GRR project (Github Repo) was created by Maxime Villard and inspired by an idea proposed by John Ellis during a talk at Defcon 2017 titled “Mountain Peak Performance: Achieving Enterprise Security at Scale.”
GRR is an open-source project that aims to provide a secure and reliable environment for anyone who uses Linux in their daily work. GRR is intended to be a complete solution that provides a secure and reliable environment while still being easy to use.
OpenCanary
OpenCanary is a free, open-source application security testing platform. It integrates with the Kubernetes API and the Prometheus monitoring system. OpenCanary can test applications for common vulnerabilities and misconfigurations by generating alerts if it detects something unusual happening in your application. In addition to its native runtime environment, OpenCanary supports other environments such as Slack, GCP Cloud Pub/Sub, AWS Lambda & Zappa.
The ethical hacker course will help you master the five steps of ethical hacking, including reconnaissance, gaining access, enumeration, maintaining access, and covering your tracks.
Cybersecurity projects to learn
- NetSecFocus: A security training platform that teaches cybersecurity basics, so you can dive deeper into specific areas of interest.
- Kali Linux: A Linux distribution used for penetration testing and security auditing because it contains hundreds of tools specifically designed for hacking, cracking, and information security research.
- Capsule8: An agentless network security platform that provides real-time visibility into threats across applications and infrastructure devices to enable an adaptive response to attacks.
- Metasploit Framework: An open-source framework used by many hackers for penetration testing purposes or simply checking whether their system has any vulnerabilities before being exploited by malicious actors online (or even by themselves).
- SUBgraph OS: A secure operating system designed from the ground up using various open-source tools focused on privacy protection, including support for hardware-based memory encryption (Intel SGX).
Conclusion
There are many cybersecurity projects that can be carried out by a team of professionals. In conclusion, many different types of cybersecurity projects can be undertaken in your organization to ensure safety from cyberattacks and other threats. The best part about these solutions is that they can be implemented without any hassles or complications at all. Opt for the ethical hacker course offered by Knowledgehut and learn ethical hacking from scratch with the comprehensive course material to become a skilled ethical hacker.
FAQs
Q1. What are current trending topics in cybersecurity?
Ans. Photos, financial transactions, emails, and texts have more potential for posing a threat to individuals than they have ever been before. Viruses or malware installed on smartphones may be one of the trends that capture the attention of cybersecurity experts in 2023.
Q2. Which country is best in cybersecurity?
Ans. Three countries have the greatest capability when it comes to cyber surveillance: China, the United States, and Russia.
Q3. What are the most common cyber-attacks in 2022?
Ans. According to an analysis of attack vectors, credential theft remains the most common attack vector, followed by phishing, misconfigured clouds, and third-party vulnerabilities. When considering how long it takes to detect and contain each type of compromise, it becomes clear how important it is to prevent these attacks.
Q4. What is the largest hack in history?
Ans. In terms of cost and destructiveness, it is considered the biggest hack in history. This attack was apparently carried out by an Iranian attack group known as the cutting sword of justice. Iranian hackers retaliated against Stuxnet with the release of Shamoon. Saudi Aramco was impacted for months by the malware, which destroyed more than 35,000 computers.
Technology
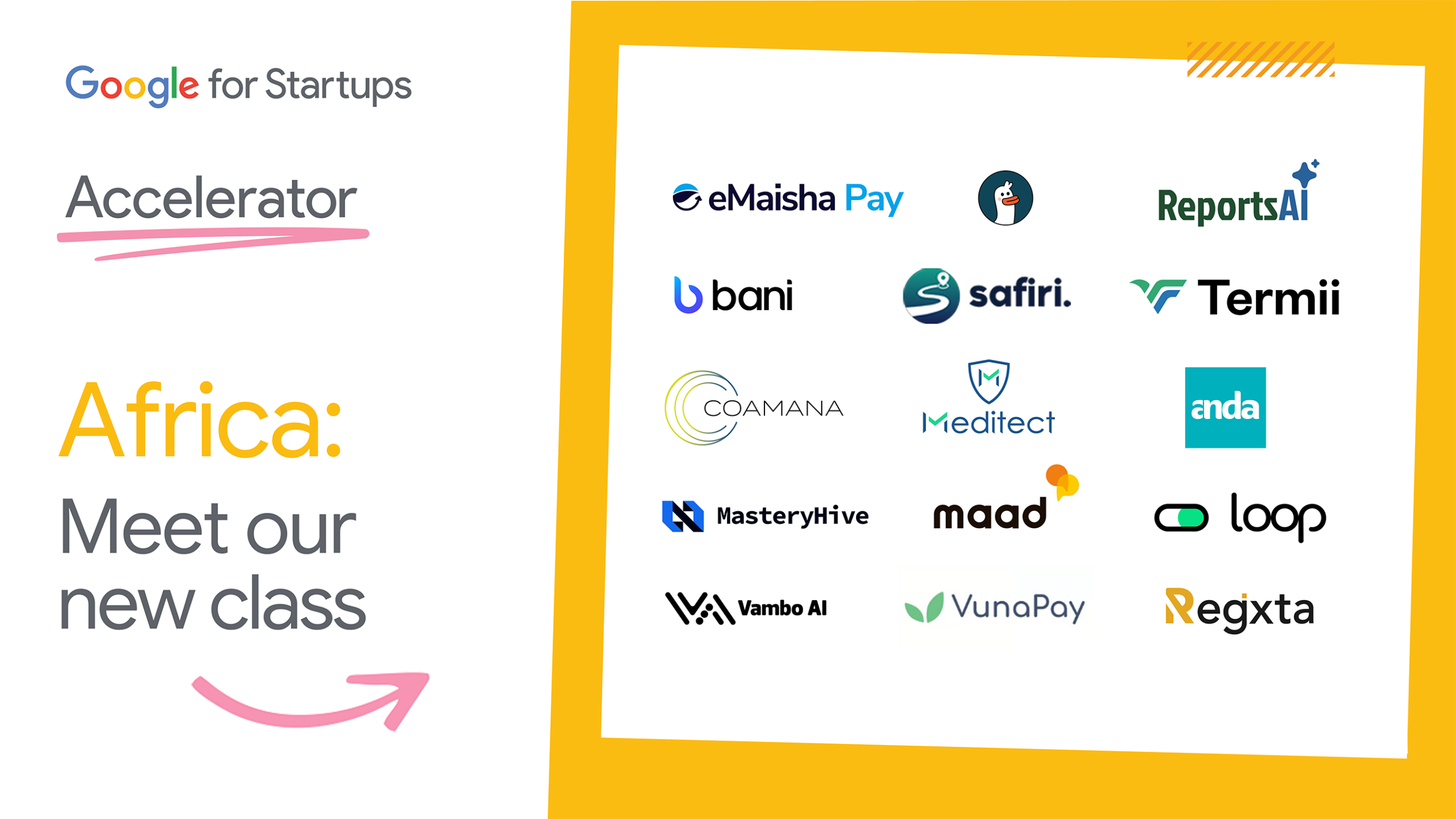
4 Nigerian Firms for 2026 Google for Startups Accelerator Africa Cohort
By Aduragbemi Omiyale
Four Nigerian firms have been selected to join the 10th Google for Startups Accelerator Africa Cohort, which began on April 13 and will end on June 19, 2026.
Fifteen companies are participating in the hybrid programme, which will receive dedicated guidance from experienced mentors and industry experts, alongside hands-on technical workshops focused on AI and machine learning.
The four Nigerian startups chosen for this scheme include Bani, MasteryHive AI, Regxta, and Termii.
They were picked from an exceptionally competitive pool of nearly 2,600 applications. The beneficiaries are utilising Artificial Intelligence (AI) to address critical local and regional challenges.
As for Bani, it is a cross-border payments infrastructure platform eliminating settlement delays for African businesses trading globally, while MasteryHive AI is an AI-native platform automating transaction reconciliation, fraud detection, and AML monitoring.
On its part, Regxta combines alternative data-driven credit scoring with a hybrid digital-agent distribution model to deliver financial products to unbanked micro businesses, while Termii uses its AI-native communications infrastructure platform to ensure reliable financial messaging for banks and fintechs.
African tech founders are actively solving fundamental infrastructural challenges, bridging gaps in financial inclusion, healthcare, and supply chains with complex AI.
The continent’s venture ecosystem showed remarkable resilience by raising $3.9 billion in 2025. However, scaling deep-tech solutions requires specialised technical infrastructure, advanced cloud capabilities, and strategic mentorship to complement this capital.
Accelerator initiatives provide these exact tools, ensuring local innovations can sustainably grow into businesses that power the continent’s digital economy.
“At Termii, we’re building AI-powered infrastructure that ensures financial transactions don’t fail, from login PINs to payment OTPs and fraud alerts.
“The Google Startup Accelerator is helping us accelerate our AI roadmap and scale globally, and even in the first week, access to technical support and insights has been incredibly valuable for our next phase of growth,” the chief executive of Termii, Mr Gbolade Emmanuel, stated.
“We are absolutely thrilled to welcome these exceptional founders into Class 10. African startups are driving essential economic growth and social development.
“Our role is to serve as a supportive partner, providing these developers and founders with the technical infrastructure, mentorship, and global network they need to scale their solutions and amplify their real-world impact,” the Head of Startup Ecosystem for Google Africa, Mr Folarin Aiyegbusi, disclosed.
Since launching in 2018, the Google for Startups Accelerator Africa program has supported 106 startups from 17 African countries, empowering them to collectively raise over $263 million and create more than 2,800 jobs.
Technology
19 Startups Pitch Solutions to Investors, Others at Demo Day in Ilorin

By Modupe Gbadeyanka
Nineteen emerging startups are being showcased at the 2026 Demo Day organised by the Ilorin Innovation Hub in partnership with IHS Nigeria, a part of IHS Holding Limited, also known as IHS Towers.
The participating small firms took part in the hub’s accelerator and incubation programmes. At this event, themed The Convergence, they will pitch their solutions to investors, venture capital funds, corporate partners, and the media.
The platform would be used to help them unlock funding opportunities, foster strategic collaborations, and amplify visibility for these startups that are developing solutions across critical sectors, including agriculture, health-tech, green energy, lifestyle, and digital services.
“We believe innovation and digital technology are powerful drivers of economic growth and sustainable development. This is why we partnered with the Kwara State Government on the Ilorin Innovation Hub.
“It is impressive and very fulfilling to see the diverse portfolio of ideas and solutions showcased today from the hub within a year of the commencement of operations. This speaks to the depth of creativity among Nigerians and what is possible when they are equipped and supported.
“Today’s event makes me proud of our investment in the space and underscores IHS Nigeria’s continued commitment to supporting technology, entrepreneurship, and digital innovation in Nigeria,” the chief executive of IHS Nigeria, Mr Mohamad Darwish, said.
The Managing Director of Ilorin Innovation Hub, Temi Kolawole, also said, “Today, we showcase 19 startups that have shown that when you combine talent with the right support, the results speak for themselves.
“The Ilorin Innovation Hub exists to ensure that geography is never a barrier to building something extraordinary, and this Demo Day is proof that we are on the right track.”
The Ilorin Innovation Hub, a partnership between the Kwara State Government and IHS Nigeria, began operations in February 2025 with programmes managed by Co-creation Hub and Future Africa.
The Demo Day presents an opportunity to take stock and assess how the Ilorin Innovation Hub is helping to nurture and bring to life groundbreaking ideas and solutions supporting economic resilience and addressing real-world societal challenges.
Technology
Lagos Tightens Cyber Defences to Attract Investment, Protect Businesses

By Adedapo Adesanya
The Lagos State Government has released a set of cybersecurity guidelines to enhance digital safety for businesses, public institutions, and residents in the state, which is home to thousands of enterprises.
A statement by the State’s Commissioner, Information and Strategy, Mr Gbenga Omotoso, noted that the development represents another decisive step in Lagos’ mission to become a secure and globally competitive digital hub.
The National Information Technology Development Agency (NITDA) estimates that Nigeria loses over $500 million (approximately N250 billion) annually to cybercrime, underscoring the urgency for stronger, coordinated security measures.
Lagos’s rapid evolution into a SMART City heightens vulnerability to cyber threats, Omotosho noted, adding that the newly issued guidelines outline clear, practical, and scalable cybersecurity best practices for small businesses, medium and large enterprises, and Ministries, Departments, and Agencies (MDAs).
They are aligned with key national frameworks, including the Cybercrime Act (2024), the Nigeria Data Protection Act (2023), and the National Cybersecurity Policy and Strategy (2021).
According to the guidelines, these recommendations are not regulatory mandates but tools designed to empower stakeholders with practical, context-specific guidance.
The Lagos State Government reaffirmed its commitment to fostering a secure digital environment that promotes innovation, investment, and public trust.
“The guidelines further strengthen Lagos State’s leadership in advancing digital trust and building a resilient, future-ready digital economy.
“The Government praised the Lagos State Cybersecurity Advisory Council, chaired by Prof. Fene Osakwe, for its strategic leadership and technical expertise in developing the framework.
“The release of these guidelines underscores Lagos State’s unwavering dedication to safeguarding digital assets, enhancing public-private collaboration, and ensuring that every organisation—from sole proprietorships to multinational corporations—can operate confidently in a secure digital environment.
“As the document highlights, A cybersecure Lagos is essential for sustaining its position as one of the most dynamic and globally competitive tech hubs of the 21st century”, the statement added.
The Lagos State Government said it will continue to refine and expand the guidelines to address emerging threats and evolving technologies, ensuring that cybersecurity remains a foundational pillar of the State’s digital transformation.
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn











1 Comment