Technology
Top Cybersecurity Projects

Introduction
Cybersecurity projects are a great way to learn more about the field and build your portfolio. They can also be fun, challenging, and rewarding—especially when you get to see what you made in action! In this article, we’ll go over some of our favorite cybersecurity projects that will help you start your journey into the industry.
The ethical hacker course from Knowledgehut will help you learn about the latest commercial-grade hacking tools, techniques, and methodologies. Pursue the course to develop cutting-edge skills and explore proven techniques and best practices to begin your career in ethical hacking.
Important Cybersecurity Projects
Some of the important cybersecurity projects are discussed below:
NetSecFocus
NetSecFocus is a community-driven cybersecurity project created as a collection of tools and resources for network security professionals. It uses open-source software where possible, with licensed content available under various licenses. The project is open to contributions from anyone interested in improving the platform by adding new features or reporting bugs.
As a GitHub repository, NetSecFocus provides source code that can be used to build your copy of the site (or just browse it online). The website is hosted using GitHub Pages to promote collaboration by making it easy for any contributor to update content on their computer before pushing changes back into central repositories shared with other contributors.
Kali Linux
Linux distribution Kali Linux was designed to be used for digital forensics and penetration testing, and it is derived from Debian. In addition to Kali Linux, Offensive Security Ltd. also develops commercial counterparts such as BlackArch and BackBox to address security concerns. It is based on Debian’s testing branch, yet at the time of writing, it was updated every three months.
The development team aims to not only provide new features but also fix bugs that they’re aware of or reported through bug trackers in each update release. Kali recently changed its name from BackTrack; both names are being used interchangeably within this article because they essentially refer to the same thing: an OS distribution with lots of hacking tools preinstalled (for example, Metasploit).
Capsule8
Capsule8 is a cloud-based security platform that provides visibility into and protection against threats in the data center. The platform enables you to protect containers, applications, and infrastructure with automatic threat detection, vulnerability scanning, and continuous monitoring of your entire containerized environment. Capsule8 can also monitor your existing Kubernetes clusters, providing security for both new and existing deployments.
Capsule8 provides a single pane of glass for security across your entire infrastructure. Capsule8’s container-native platform enables you to automatically detect and respond to threats in real time, including vulnerabilities, malware, and data breaches. You can also use Capsule8 to continuously monitor your environment for signs of compromise and remediate issues before they become serious problems.
Metasploit Framework
The Metasploit Framework is a tool that helps you find and exploit security vulnerabilities in networks. It is a framework that security professionals, penetration testers, and hackers can use. HD Moore created the Metasploit Framework in 2003 to help automate tasks for network administrators and security consultants, but it has since been expanded to include a huge community that contributes code and new modules all the time.
The Metasploit Framework allows you to write your scripts, called modules. These can be used to perform a wide range of tasks, from scanning for vulnerabilities in a network to exploiting those vulnerabilities and gaining access. The software also comes with a database of pre-written tools that can be used right away.
SUBgraph OS
SUBgraph OS is a Linux-based operating system designed to be resistant to cyberattacks. It was developed by a team of security researchers, who are also the founders of SUBnet Labs, which developed SUBgraph OS as part of their research into information security. The developers describe SUBgraph as “a privacy-focused operating system” protected by “hosted virtualization” and an “isolated hypervisor.”
It means that while it’s based on the Linux kernel like other operating systems (such as Ubuntu), it doesn’t share any code with those other systems. It uses virtualization to create an isolated container where dangerous processes cannot access your data on the hard drive.
Google Grr
Google Grr is a collection of tools that help you detect and respond to advanced threats. The project was released in May 2018 by Google and MITRE with the intent to make the GRR tool available for Linux users.
The open-source GRR project (Github Repo) was created by Maxime Villard and inspired by an idea proposed by John Ellis during a talk at Defcon 2017 titled “Mountain Peak Performance: Achieving Enterprise Security at Scale.”
GRR is an open-source project that aims to provide a secure and reliable environment for anyone who uses Linux in their daily work. GRR is intended to be a complete solution that provides a secure and reliable environment while still being easy to use.
OpenCanary
OpenCanary is a free, open-source application security testing platform. It integrates with the Kubernetes API and the Prometheus monitoring system. OpenCanary can test applications for common vulnerabilities and misconfigurations by generating alerts if it detects something unusual happening in your application. In addition to its native runtime environment, OpenCanary supports other environments such as Slack, GCP Cloud Pub/Sub, AWS Lambda & Zappa.
The ethical hacker course will help you master the five steps of ethical hacking, including reconnaissance, gaining access, enumeration, maintaining access, and covering your tracks.
Cybersecurity projects to learn
- NetSecFocus: A security training platform that teaches cybersecurity basics, so you can dive deeper into specific areas of interest.
- Kali Linux: A Linux distribution used for penetration testing and security auditing because it contains hundreds of tools specifically designed for hacking, cracking, and information security research.
- Capsule8: An agentless network security platform that provides real-time visibility into threats across applications and infrastructure devices to enable an adaptive response to attacks.
- Metasploit Framework: An open-source framework used by many hackers for penetration testing purposes or simply checking whether their system has any vulnerabilities before being exploited by malicious actors online (or even by themselves).
- SUBgraph OS: A secure operating system designed from the ground up using various open-source tools focused on privacy protection, including support for hardware-based memory encryption (Intel SGX).
Conclusion
There are many cybersecurity projects that can be carried out by a team of professionals. In conclusion, many different types of cybersecurity projects can be undertaken in your organization to ensure safety from cyberattacks and other threats. The best part about these solutions is that they can be implemented without any hassles or complications at all. Opt for the ethical hacker course offered by Knowledgehut and learn ethical hacking from scratch with the comprehensive course material to become a skilled ethical hacker.
FAQs
Q1. What are current trending topics in cybersecurity?
Ans. Photos, financial transactions, emails, and texts have more potential for posing a threat to individuals than they have ever been before. Viruses or malware installed on smartphones may be one of the trends that capture the attention of cybersecurity experts in 2023.
Q2. Which country is best in cybersecurity?
Ans. Three countries have the greatest capability when it comes to cyber surveillance: China, the United States, and Russia.
Q3. What are the most common cyber-attacks in 2022?
Ans. According to an analysis of attack vectors, credential theft remains the most common attack vector, followed by phishing, misconfigured clouds, and third-party vulnerabilities. When considering how long it takes to detect and contain each type of compromise, it becomes clear how important it is to prevent these attacks.
Q4. What is the largest hack in history?
Ans. In terms of cost and destructiveness, it is considered the biggest hack in history. This attack was apparently carried out by an Iranian attack group known as the cutting sword of justice. Iranian hackers retaliated against Stuxnet with the release of Shamoon. Saudi Aramco was impacted for months by the malware, which destroyed more than 35,000 computers.
Technology
Meta Expands Business Agent to Instagram, WhatsApp, Messenger
By Aduragbemi Omiyale
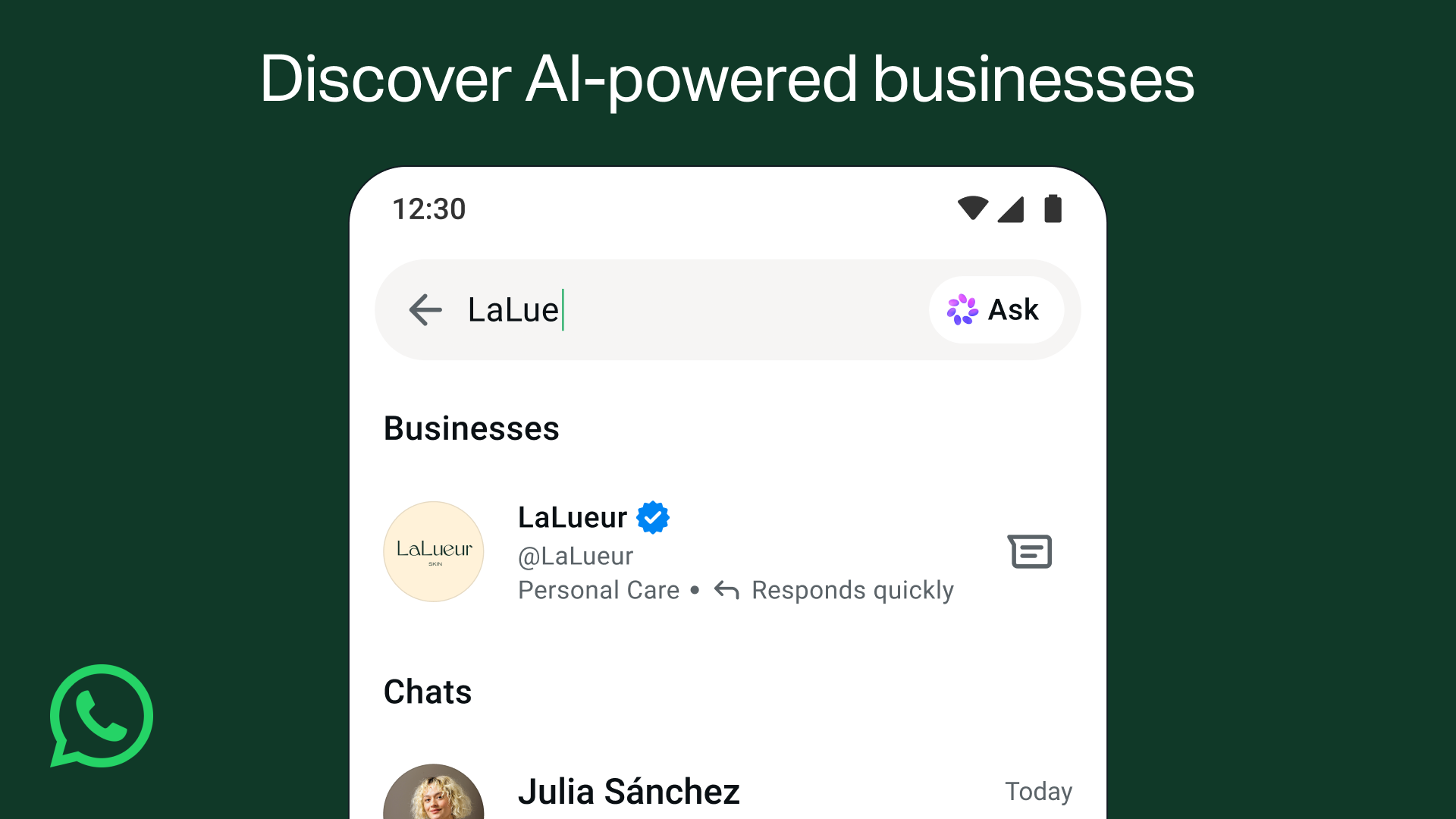
The reach of the Meta Business Agent is being expanded to Instagram and other platforms of the social media giant.
Meta Business Agent is an artificial intelligence (AI) that allows business owners to attend to customers’ needs with ease.
Customers expect instant responses, but no team can be everywhere at once. This innovation handles such without hassles.
It helps businesses to answer questions specific to the business, makes product recommendations from the catalogue, books appointments, qualifies incoming leads, and closes sales.
More than one million businesses are already using a Meta Business Agent on WhatsApp and Messenger to respond to customers around the clock.
“We’re now expanding our Business Agent to businesses big and small globally, so within minutes you can have yours up and running, responding in your customer’s local language using your tone,” Meta said in a statement.
“We’re also expanding these agents to Instagram since businesses connect with their customers there, too. Businesses can activate their Business Agent here. Getting started with the Business Agent is free. In the coming months, businesses will access the agent through our paid subscription offerings, with options for businesses of every size,” it added.
Meta also stated that it is making it simpler for people to discover businesses powered by a Meta Business Agent directly on WhatsApp. It noted that starting soon, people will be able to find businesses by typing their name in the Search bar, or by sharing their phone number or contact card in chats with friends and family. This way, when more customers reach out, they get a quick, helpful response.
Technology
Lagos Eyes 250MW Data Centre Capacity by 2030
By Adedapo Adesanya
The Lagos State government plans to expand the city’s data centre capacity to over 250 megawatts (MW) by 2030 as part of efforts to strengthen its digital infrastructure ecosystem.
This was disclosed by the state’s Commissioner for Innovation, Science, and Technology, Mr Olatubosun Alake, at the launch of the Kasi Cloud LOS1 data centre facility in Lekki. Nigeria Sovereign Investment Authority (NSIA) invested in Kasi Cloud through an $8 million convertible loan note in 2021.
Mr Alake said Lagos already hosts nearly three-quarters of Nigeria’s commercial data centre capacity, adding that the government intends to expand its infrastructure footprint significantly over the next five years.
“There are about 146 additional megawatt data centres planned in the pipeline,” he said. “We envisage that by 2030, we would have over 250 megawatts of data centre capacity in Lagos, three times the current capacity growth.”
The expansion comes as demand for cloud services, AI computing power, and local data storage continues to grow across Nigeria’s digital economy, with Lagos at the forefront, housing thousands of businesses and startups.
Mr Alake said the Kasi Cloud facility represents Lagos’ entry into “large-scale hyperscale AI infrastructure,” signalling the state’s ambition to evolve beyond being known primarily as a startup hub into a major centre for digital infrastructure and AI computing.
“Lagos is no longer simply a startup city,” he said. “It is an infrastructure city.”
The Kasi LOS1 facility is designed as a 40MW hyperscale data centre campus, beginning operations with an initial 7.2MW IT load.
According to Mr Alake, the facility includes advanced GPU computing infrastructure powered by Nvidia H100 and H200 chips, alongside liquid cooling systems and cloud infrastructure services designed to support AI workloads.
The Lagos State government believes such infrastructure will become critical as AI adoption accelerates globally.
Mr Alake said the state is investing in fibre optic networks, smart city technologies, university innovation programmes, and digital government systems to prepare for the transition.
“The AI economy is going to require hundreds of megawatts,” he said. “The market has already made its decision about where digital infrastructure belongs.”
On his part, Mr Johnson Agbogun, co-founder and chief executive officer of Kasi Cloud, said the project was built to reduce Nigeria’s dependence on foreign cloud infrastructure and give African businesses more control over how their data and AI systems are developed.
“Nigerian enterprises are currently spending $850 million every year on foreign cloud infrastructure,” he said. “Every naira spent abroad on cloud and AI infrastructure helps build capabilities somewhere else.”
He added that the facility runs GPU-powered AI workloads from local enterprises and described the Lekki campus as “the beginning of Nigeria’s AI factory.”
“As artificial intelligence reshapes economies globally, the nations that control their own compute infrastructure and data will be the ones positioned to lead,” added Mr Kolawole Owodunni, NSIA’s Executive Director and Chief Information Officer.
Technology
Google I/O 2026: 4 Major Updates That Are Changing How Google Search Works

The goal of Google Search has always been simple: to help you ask anything on your mind. Whether it is a quick fact to help with your daily hustle or a complex question about starting a new business, Nigerians rely on Search every single day.
Over the last year, Google has rapidly reimagined what Search can do with AI. The momentum has been incredible—just one year after its debut, AI Mode has surpassed one billion monthly users globally. As people have realised just how much more Search can do for them, they are searching more than ever before, reaching an all-time high in search queries last quarter. Today at Google I/O, Google shared the next step in its journey to bring together the best of a search engine with the best of AI.
To power this next chapter, Google is officially upgrading Search with Gemini 3.5 Flash as the new default model in AI Mode for everyone worldwide. Delivering sustained frontier performance for agents and coding, Gemini 3.5 Flash is the engine driving the new era of AI-powered Search. Because curiosity doesn’t always fit into standard keywords, this powerful AI model is transforming Search from a tool that simply finds information into an intelligent platform capable of reasoning, monitoring the web, and executing complex tasks on your behalf.
Here is a look at the four biggest AI-powered announcements coming to Google Search:
1. A Completely Reimagined Search Box
Google is introducing the biggest upgrade to its Search box in over 25 years. Now completely reimagined with AI, the new intelligent Search box dynamically expands to give you the space to describe exactly what you need. It goes beyond simple autocomplete by anticipating your intent and helping you phrase your questions. You are no longer limited to typing; you can now search using text, images, files, videos, or even Chrome tabs as inputs. Additionally, Google is making it easier to ask follow-up questions directly from an AI Overview, flowing naturally into a conversational back-and-forth where your context stays with you as you explore.
2. New Search Agents That Work in the Background
We are entering the era of Search agents, where you can create and manage multiple AI agents directly in Search. Google is launching “Information agents” that operate in the background 24/7. These agents intelligently scan the web—alongside fresh data on finance, shopping, and sports—to monitor for changes related to your specific questions. For example, if you are house hunting, your agent will continuously scan the market and notify you the moment a listing matches your exact criteria. Furthermore, Search is expanding its agentic booking capabilities; you can soon share specific criteria (like a late-night private karaoke room) and Search will pull the latest pricing and links to finish booking. For certain categories, Google can even call businesses on your behalf.
3. Custom Mini-Apps and Visuals Built Just for You
Search is no longer just returning links; it is now building the ideal response in the perfect format for your query entirely on the fly. By bringing the power of Google Antigravity and the agentic coding capabilities of Gemini 3.5 Flash into Search, users will get a custom “Generative UI.” This means Search can design custom layouts, interactive visuals, tables, graphs, or simulations in real-time. But it goes a step further: if you have an ongoing task, like establishing a new health routine, Search can actually code a custom fitness tracker or mini-app for you. These custom dashboards tap into real-time sources like live maps and weather, giving you a personalised tracker you can return to again and again.
4. Expanded Personal Intelligence Without a Subscription
For AI to be truly helpful, it shouldn’t just know the world’s information—it should understand your personal context, too. To achieve this, Google is expanding Personal Intelligence in AI Mode to more people in nearly 200 countries and territories across 98 languages. Crucially, this is being rolled out with no subscription required. Users can securely connect apps like Gmail, Google Photos, and soon Google Calendar directly to Search. Designed with transparency and choice at its heart, this allows you to safely ask Search to find information buried in your own personal files, always keeping you in complete control of your connected data.
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn











1 Comment