Feature/OPED
The North-South Political Alliance and the Unending Intrigues of Power

By Wole Arisekola
Frantically, I have never been desperate for anything all my life. Never! And how I wish everyone can honestly say so about themselves.
Most Nigerians are very desperate to acquire money, fame and political power.
I think the idea of getting something at all cost can drive one crazy, leading someone to make decisions that can stop him or her from making heaven and drive out all the rational thoughts from a person’s brain.
I appreciate the word ‘consistency’ and I am conscious of the word ‘loyalty’.
But to be frank, the politics of alliance with our brothers in the Northern part of Nigeria always comes with a price.
Let me take you down memory lane; when Chief S.L Akintola formed an alliance with the Northern Party, National Council of Nigeria and the Cameroons (NCNC) against Chief Awolowo’s Action Group, majority of the people in Awolowo’s camp incited the Yorubas against him. They turned his people against him.
All the good things he was known for were forgotten. He was assassinated in the coup that followed that election.
Another example was Alhaji Lateef Jakande; he was the most popular among the governors elected on the platform of the Unity Party of Nigeria in the Second Republic. He was referred to as Baba Kekere, meaning second in command to Chief Obafemi Awolowo.
When the military took over and he was nominated as a Minister, many Yoruba people went against it. He was told not to have anything to do with the military government. He went against the opinion of the Yorubas and his political career was destroyed till today. He lost his relevance in Yoruba politics.
Chief Moshood Kashimawo Olawale Abiola will serve as my third example.
Late MKO Abiola was a successful businessman and a detribalised Nigerian. As a philanthropist, he was unrivalled. He was generous to a fault. His sin in Yorubaland before he died was that he associated himself with the National Party of Nigeria (NPN) which was seen by many in the South West as a Northern party against their beloved UPN.
Chief Abiola was not accepted politically in the South West before the military annulled his election.
National Democratic Coalition (NADECO) was formed after Chief Abiola’s election was annulled by the General Babangida regime.
Chief Abiola eventually died in military custody in 1998 while fighting for both his freedom and the actualisation of his mandate.
Aare Abdulazeez Arisekola Alao makes the fourth example and what actually happened to Asiwaju Ahmed Tinubu last week is like child’s play compared to what Arisekola went through during his lifetime for being in support of Northerners in the South West.
Late Aare Arisekola was nearly killed at the University of Ibadan by the well-organised political thugs who infiltrated the students on the campus of the University of Ibadan.
About 23 of his exotic cars were burnt to ashes. Despite being guarded by the best security operatives in the world, he sustained a deep cut on his head.
Not satisfied, the mob went to his companies in Ibadan and Lagos and burned them down.
A month before that incident, Aare had sent a message to Akolad, his contractor and father of former Commissioner of Finance under Senator Ajimobi, Bimbo Adekanbi.
He asked Akolad to go and renovate and fortify his office.
It was as if he knew that something of that nature would happen. He travelled abroad and over 100 exotic cars were parked inside his office. His business partner, Mr Tribute, was around and some cash were kept in the office for the day to day activities of running the business. All these were burnt down to nothing.
Arisekola Alao lost over 150 cars and property worth billions of Naira as his properties were torched.
When his friend realised this monumental loss, he ordered the federal government to pay him a compensation of N100 million. The money was paid and lodged in United Bank for Africa.
Trust Aare Arisekola Alao, he did not touch it. He kept it with the bank. When Chief Obasanjo came to power and he was investigating the Sani Abacha regime, he sent security agents to Arisekola in Ibadan to demand the N100 million the federal government paid him when his properties were burnt.
Aare instructed me (Wole) to follow his brother, Akeem to UBA at Dugbe in Ibadan to prepare a N100 million draft in the name of the federal government and give it to the security agents who came from Abuja.
Not yet satisfied, they told Aare that they have instruction from the Presidency to bring his international passport and all his travel documents, he went inside and when Aare came out, he handed them over.
It will be in history that President Obasanjo kept Aare’s travelling documents with him all through his eight years in office.
When he left office as President, he brought it back to him and he told Aare jokingly that “I just want you to be in Nigeria with me throughout my stay in power. I kept your passport inside my drawer for eight years!”
Till today, no one has thought of returning this money to Arisekola Alao’s family. Strange, isn’t it?
There is always a price to pay if you are a Yoruba politician associating with Northern politicians.
But now that, Asiwaju Ahmed Tinubu is on the hot seat. He is the one who sold Buhari to Yorubas. Some Yorubas don’t like that idea. The Afenifere didn’t want to hear anything about Buhari because of his past record. How Asiwaju muscled down this group and gained trust among Yorubas to support Buhari is still a mystery to me.
The well-fortified Yoruba regional party, Alliance for Democracy (AD), was annihilated to pave way for a smooth alliance with Buhari’s party.
The progressives were not happy. They didn’t like to join a Northern party. They saw Asiwaju Bola Tinubu as a traitor and they have been waiting for the day they would take their pound of flesh from him.
The opportunity came when there was a crack among the new political family of Asiwaju Tinubu. They watched, arms folded, faces turned to the other side as Tinubu faced his fate alone. No single press release from Afenifere and Yoruba elders. They simply maintained their “we warned him” stand.
To them, he drove himself to the belly of vultures and he must pay the price like his past leaders who dared to against their will.
What happened last week was more than a protest. It was a repeat of history.
If you are a Yoruba man and you are into politics, be careful. Read Yoruba politics before you jump into any alliance. And if you are to do so, consult widely.
Asiwaju Bola Ahmed Tinubu has entered the political ocean of the South-West-North. He is in the middle now, only God knows where it will lead him to.
As for me, and my family, we will continue and continue to pray for him; for turning boys to men, for bringing some development to our region. Although to many of us, he is not perfect, neither is any of us.
But I am pleading with our fathers and brothers to please forgive him of any sin – big or small – he might have committed as a person in the name politics.
We should please follow our fathers’ proverb; ti a ba fi owo otun ba omo wi, a ma nfi isi fa mo ra ni (if we reprimand a child with the right hand, we should embrace him with the left).
Ire ooo, emi ni omo yin ni tooto.
Wole Arisekola is a journalist and the publisher of Streetjournal.com
Feature/OPED
Why President Tinubu Must End Retirement Age Disparity Between Medical and Veterinary Doctors Now

By James Ezema
To argue that Nigeria cannot afford policy inconsistencies that weaken its already fragile public health architecture is not an exaggeration. The current disparity in retirement age between medical doctors and veterinary professionals is one such inconsistency—one that demands urgent correction, not bureaucratic delay.
The Federal Government’s decision to approve a 65-year retirement age for selected health professionals was, in principle, commendable. It acknowledged the need to retain scarce expertise within a critical sector. However, by excluding veterinary doctors and veterinary para-professionals—whether explicitly or by omission—the policy has created a dangerous gap that undermines both equity and national health security.
This is not merely a professional grievance; it is a structural flaw with far-reaching consequences.
At the heart of the issue lies a contradiction the government cannot ignore. For decades, Nigeria has maintained a parity framework that places medical and veterinary doctors on equivalent footing in terms of salary structures and conditions of service. The Consolidated Medical Salary Structure (CONMESS) framework recognizes both professions as integral components of the broader health ecosystem. Yet, when it comes to retirement policy, that parity has been abruptly set aside.
This inconsistency is indefensible.
Veterinary professionals are not peripheral actors in the health sector—they are central to it. In an era defined by zoonotic threats, where the majority of emerging infectious diseases originate from animals, excluding veterinarians from extended service retention is not only unfair but strategically reckless.
Nigeria has formally embraced the One Health approach, which integrates human, animal, and environmental health systems. But policy must align with principle. It is contradictory to adopt One Health in theory while sidelining a core component of that framework in practice.
Veterinarians are at the frontline of disease surveillance, outbreak prevention, and biosecurity. They play critical roles in managing threats such as anthrax, rabies, avian influenza, Lassa fever, and other zoonotic diseases that pose direct risks to human populations. Their contribution to safeguarding the nation’s livestock—estimated in the hundreds of millions—is equally vital to food security and economic stability.
Yet, at a time when their relevance has never been greater, policy is forcing them out prematurely.
The workforce realities make this situation even more alarming. Nigeria is already grappling with a severe shortage of veterinary professionals. In some states, only a handful of veterinarians are available, while several local government areas have no veterinary presence at all. Compelling experienced professionals to retire at 60, while their medical counterparts remain in service until 65, will only deepen this crisis.
This is not a theoretical concern—it is an imminent risk.
The case for inclusion has already been made, clearly and responsibly, by the Nigerian Veterinary Medical Association and the Federal Ministry of Livestock Development. Their position is grounded in logic, policy precedent, and national interest. They are not seeking special treatment; they are demanding consistency.
The current circular, which limits the 65-year retirement age to clinical professionals in Federal Tertiary Hospitals and excludes those in mainstream civil service structures, is both administratively narrow and strategically flawed. It fails to account for the unique institutional placement of veterinary professionals, who operate largely outside hospital settings but are no less critical to national health outcomes.
Policy must reflect function, not merely location.
This is where decisive leadership becomes imperative. The responsibility now rests squarely with Bola Ahmed Tinubu to address this imbalance and restore coherence to Nigeria’s health and civil service policies.
A clear directive from the President to the Office of the Head of the Civil Service of the Federation can correct this anomaly. Such a directive should ensure that veterinary doctors and veterinary para-professionals are fully integrated into the 65-year retirement framework, in line with existing parity policies and the realities of modern public health.
Anything less would signal a troubling disregard for a sector that plays a quiet but indispensable role in national stability.
This is not just about fairness—it is about foresight. Public health security is interconnected, and weakening one component inevitably weakens the entire system.
Nigeria stands at a critical juncture, confronted by complex health, food security, and economic challenges. Retaining experienced veterinary professionals is not optional; it is essential.
The disparity must end—and it must end now.
Comrade James Ezema is a journalist, political strategist, and public affairs analyst. He is the National President of the Association of Bloggers and Journalists Against Fake News (ABJFN), National Vice-President (Investigation) of the Nigerian Guild of Investigative Journalists (NGIJ), and President/National Coordinator of the Not Too Young To Perform (NTYTP), a national leadership development advocacy group. He can be reached via email: [email protected] or WhatsApp: +234 8035823617.
Feature/OPED
N4.65 trillion in the Vault, but is the Real Economy Locked Out?

By Blaise Udunze
Following the successful conclusion of the banking sector recapitalisation programme initiated in March 2024 by the Central Bank of Nigeria, the industry has raised N4.65 trillion. No doubt, this marks a significant milestone for the nation’s financial system as the exercise attracted both domestic and foreign investors, strengthened capital buffers, and reinforced regulatory confidence in the banking sector. By all prudential measures, once again, it will be said without doubt that it is a success story.
Looking at this feat closely and when weighed more critically, a more consequential question emerges, one that will ultimately determine whether this achievement becomes a genuine turning point or merely another financial milestone. Will a stronger banking sector finally translate into a more productive Nigerian economy, or will it be locked out?
This question sits at the heart of Nigeria’s long-standing economic contradiction, seeing a relatively sophisticated financial system coexisting with weak industrial output, low productivity, and persistent dependence on imports truly reflects an ironic situation. The fact remains that recapitalisation, by design, is meant to strengthen banks, enhancing their ability to absorb shocks, manage risks and support economic growth. According to the apex bank, the programme has improved capital adequacy ratios, enhanced asset quality, and reinforced financial stability. Under the leadership of Olayemi Cardoso, there has also been a shift toward stricter risk-based supervision and a phased exit from regulatory forbearance.
These are necessary reforms. A stable banking system is a prerequisite for economic development. However, the truth be told, stability alone is not sufficient because the real test of recapitalisation lies not in stronger balance sheets, but in how effectively banks channel capital into productive economic activity, sectors that create jobs, expand output and drive exports. Without this transition, recapitalisation risks becoming an exercise in financial strengthening without economic transformation.
Encouragingly, early signals from industry experts suggest that the next phase of banking reform may begin to address this long-standing gap. Analysts and practitioners are increasingly pointing to small and medium-sized enterprises (SMEs) as a key destination for recapitalisation inflows, which is a fact beyond doubt. Given that SMEs account for over 70 per cent of registered businesses in Nigeria, the logic is compelling. With great expectation, as has been practicalised and established in other economies, a shift in credit allocation toward this segment could unlock job creation, stimulate domestic production, and deepen economic resilience. Yet, this expectation must be balanced with reality. Historically, and of huge concern, SMEs have received only a marginal share of total bank credit, often due to perceived risk, lack of collateral, and weak credit infrastructure.
Indeed, Nigeria’s broader financial intermediation challenge remains stark. Even as the giant of Africa, private sector credit stands at roughly 17 per cent of GDP, and this is far below the sub-Saharan African average, while SMEs receive barely 1 per cent of total bank lending despite contributing about half of GDP and the vast majority of employment. These figures underscore the structural disconnect between the banking system and the real economy. Recapitalisation, therefore, must be judged not only by the strength of banks but by whether it meaningfully improves this imbalance.
Nigeria’s economic challenge is not merely one of capital scarcity; it is fundamentally a problem of low productivity. Manufacturing continues to operate far below capacity, agriculture remains largely subsistence-driven, and industrial output contributes only modestly to GDP. Despite decades of banking sector expansion, credit to the real sector has remained limited relative to the size of the economy. Instead, banks have often gravitated toward safer and more profitable avenues such as government securities, treasury instruments, and short-term trading opportunities.
This is not irrational. It reflects a rational response to risk, policy signals, and market realities. However, it has created a structural imbalance in which capital circulates within the financial system without sufficiently reaching the productive economy. The result is a pattern where financial sector growth outpaces real sector development, a phenomenon widely described as financialisation without productivity gains.
At the centre of this challenge is the issue of credit allocation. A recapitalised banking sector, strengthened by new capital and improved buffers, should theoretically expand lending. But this is, contrarily, because the more important question is where that lending will go. Will Nigerian banks extend long-term credit to manufacturers, finance agro-processing and value chains, and support scalable SMEs, or will they continue to concentrate on low-risk government debt, prioritise foreign exchange-related gains, and maintain conservative lending practices in the face of macroeconomic uncertainty? Some of these structural questions call for immediate answers from policymakers.
Some industry voices are optimistic that the expanded capital base will translate into a broader loan book, increased investment in higher-risk sectors, and improved product offerings for depositors; this is not in doubt. There are also expectations that banks will scale operations across the continent, leveraging stronger balance sheets to expand their regional footprint. Yes, they are expected, but one thing that must be made known is that optimism alone does not guarantee transformation. The fact is that without deliberate incentives and structural reforms, capital may continue to flow toward low-risk assets rather than high-impact sectors.
Beyond lending, experts are also calling for a shift in how banking success is measured. The next phase of reform, according to the experts in their arguments, must move from capital thresholds to customer outcomes. This includes stronger consumer protection frameworks, real-time complaint management systems and more transparent regulatory oversight. A more technologically driven supervisory model, one that allows regulators to monitor customer experiences and detect systemic risks early, could play a critical role in strengthening trust and accountability within the system.
This dimension is often overlooked but deeply significant. A banking system that is well-capitalised but unresponsive to customer needs risks undermining public confidence. True financial development is not only about capital strength but also about accessibility, fairness, and service quality. Nigerians must feel the impact of recapitalisation not just in improved financial ratios, but in better banking experiences, more inclusive services, and greater economic opportunity.
The recapitalisation exercise has also attracted notable foreign participation, signalling confidence in Nigeria’s banking sector. However, confidence in banks does not necessarily translate into confidence in the broader economy. The truth is that foreign investors are typically drawn to strong regulatory frameworks, attractive returns, and market liquidity, though the facts are that these factors make Nigerian banks appealing financial assets; it must be made explicitly clear that they do not automatically reflect confidence in the country’s industrial base or productivity potential.
This distinction is critical. An economy can attract capital into its financial sector while still struggling to attract investment into productive sectors. When this happens, growth becomes financially driven rather than fundamentally anchored. The risk, therefore, is that recapitalisation could deepen Nigeria’s financial markets, but what benefits or gains when banks become stronger or liquid without addressing the structural weaknesses of the real economy.
It is clear and explicit that the current policy direction of the CBN reflects a strong emphasis on stability, with tightened supervision, improved transparency, and stricter prudential standards. These measures are necessary, particularly in a volatile global environment. However, there is an emerging concern that stability may be taking precedence over growth stimulation, which should also be a focal point for every economy, of which Nigeria should not be left out of the equation. Central banks in emerging markets often face a delicate balancing act, and this is putting too much focus on stability, which can constrain credit expansion, while too much emphasis on growth can undermine financial discipline, as this calls for a balance.
In Nigeria’s case, the question is whether sufficient mechanisms exist to align banking sector incentives with national productivity goals. Are there enough incentives to encourage long-term lending, sector-specific financing, and innovation in credit delivery? Or does the current framework inadvertently reward risk aversion and short-term profitability?
Over the past two decades, it has been a herculean experience as Nigeria’s economic trajectory suggests a growing disconnect between the financial sector and the real economy. Banks have become larger, more sophisticated and more profitable, yet the irony is that the broader economy continues to struggle with high unemployment, low industrial output, and limited export diversification. This divergence reflects the structural risk of financialization, a condition in which financial activities expand without a corresponding increase in real economic productivity.
If not carefully managed, recapitalisation could reinforce this trend. With more capital at their disposal, banks may simply scale existing business models, expanding financial activities that generate returns without contributing meaningfully to production. The point is that this is not solely a failure of the banking sector; it is a systemic issue shaped by policy design, regulatory priorities, and market incentives, which needs the urgent attention of policymakers.
Meanwhile, for recapitalisation to achieve its intended purpose and truly work, it must be accompanied by a deliberate shift or intentional policy change from capital accumulation to productivity enhancement and the economy to produce more goods and services efficiently. This begins with creating stronger incentives for real sector lending with differentiated capital requirements based on sector exposure, credit guarantees for high-impact industries, and interest rate support for priority sectors, which can encourage banks to channel funds into productive areas, and this must be driven and implemented by the apex bank to harness the gains of recapitalisation.
This transformative process is not only saddled with the CBN, but the Development finance institutions also have a critical role to play in de-risking long-term investments, making it easier for commercial banks to participate in financing projects that drive economic growth. At the same time, one of the missing pieces that must be taken into cognisance is that regulatory frameworks should discourage excessive concentration in risk-free assets. No doubt, banks thrive in profitability, as government securities remain important; overreliance on them can crowd out private sector credit and limit economic expansion.
Innovation in financial products is equally essential. Traditional lending models often fail to meet the needs of SMEs and emerging industries, as this has continued to hinder growth. Banks must explore new approaches, including digital lending platforms, supply chain financing, and blended finance solutions that can unlock new growth opportunities, while they extend their tentacles by saturating the retail space just like fintech.
Accountability must also be embedded in the system. One fact is that if recapitalisation is justified as a tool for economic growth, then its outcomes and gains must be measurable and not obscure. Increased credit to productive sectors, higher industrial output and job creation should serve as key indicators of success. Without such metrics, the exercise risks being judged solely by financial indicators rather than its real economic impact.
The completion of the recapitalisation programme represents more than a regulatory achievement; it is a defining moment for Nigeria’s economic future. The country now has a banking sector that is better capitalised, more resilient, and more attractive to investors. These are important gains, but they are not ends in themselves.
The ultimate objective is to build an economy that is productive, diversified, and inclusive. Achieving this requires more than strong banks; it requires banks that actively power economic transformation.
The N4.65 trillion recapitalisation is a significant step forward. It strengthens the foundation of Nigeria’s financial system and enhances its capacity to support growth. However, capacity alone is not enough and truly not enough if the gains of recapitalisation are to be harnessed to the latter. What matters now is how that capacity is deployed.
Some of the critical questions for urgent attention are as follows: Will banks rise to the challenge of financing Nigeria’s productive sectors, particularly SMEs that form the backbone of the economy? Will policymakers create the right incentives to ensure credit flows where it is most needed? Will the financial system evolve from a focus on profitability to a broader commitment to the economic purpose of fostering a more productive Nigerian economy and the $1 trillion target?
The above questions are relevant because they will determine whether recapitalisation becomes a catalyst for change or a missed opportunity if not taken into cognisance. A well-capitalised banking sector is not the destination; it is the starting point. The real journey lies in building an economy where capital works, productivity rises, and growth becomes both sustainable and inclusive.
Blaise, a journalist and PR professional, writes from Lagos and can be reached via: [email protected]
Feature/OPED
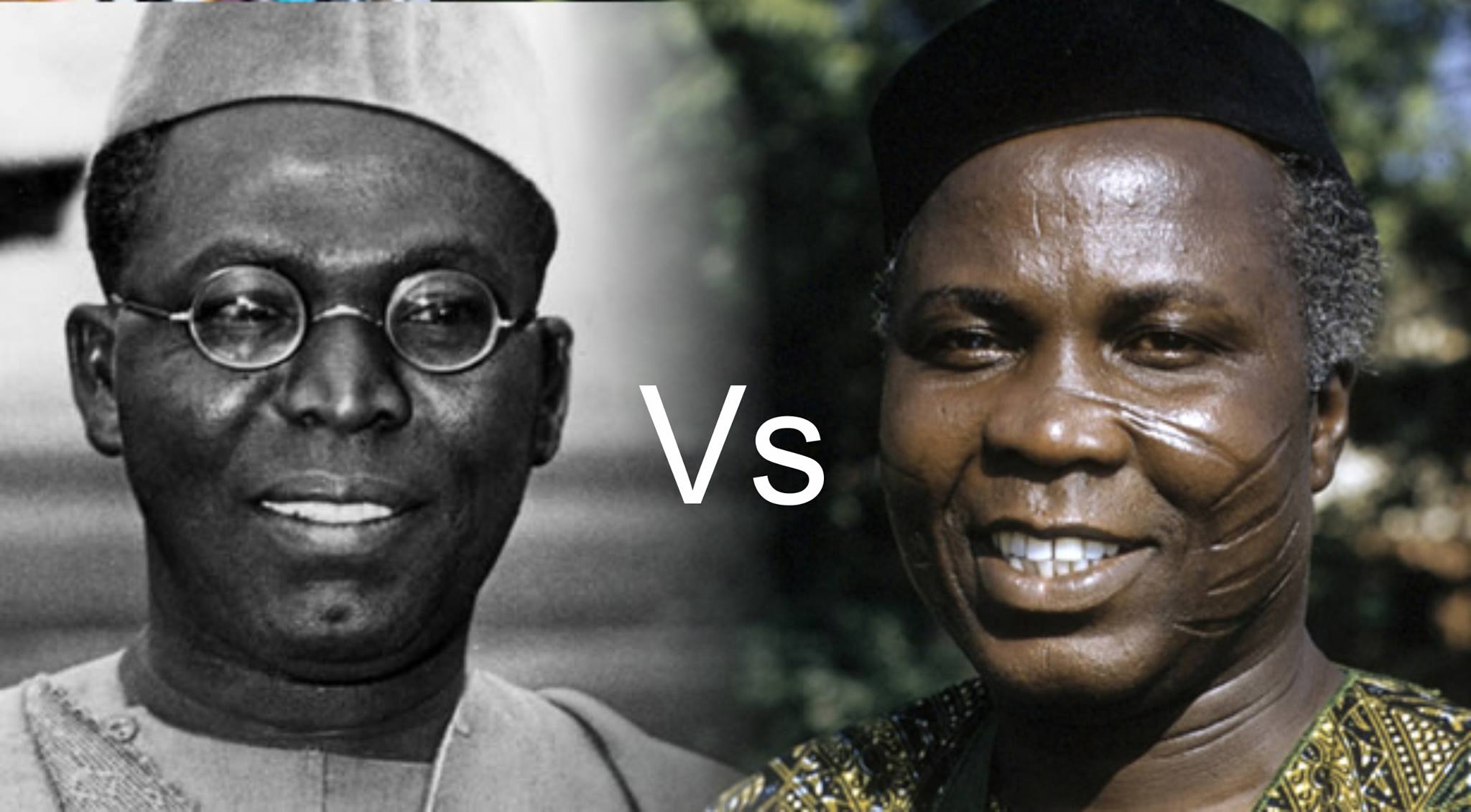
Akintola vs Awolowo, Opposition, and the One-Party Temptation
By Prince Charles Dickson, PhD
Every generation of Nigerian politics likes to imagine that its quarrel is unprecedented, that its betrayals are original, that its intrigue is wearing a crown no earlier intrigue ever touched. But Nigerian politics is an old drummer. It changes songs, not rhythm. The names change. The costumes improve. The microphones get better. Yet the same questions keep returning like harmattan dust: What is opposition for? Is it a moral force, a strategic waiting room, or merely a branch office of the ruling instinct?
To ask that question seriously is to walk back into the haunted chamber of Awolowo and Akintola. What began as a struggle inside the Action Group was not just a disagreement between two brilliant men. It was a collision of political temperaments, ideological direction, ambition, and the larger architecture of power in Nigeria. Awolowo, who moved to the federal centre as opposition leader after 1959, was increasingly identified with a broader ideological project. Akintola, by contrast, came to embody a more conservative, region-focused and business-oriented current, and his openness to working with the Northern-dominated federal establishment deepened the rupture. By mid-1962, Awolowo’s camp had repudiated Akintola; the federal government declared a state of emergency in the Western Region and restored him in 1963. The bitterness of that split, and the wreckage that followed, helped poison the First Republic.
That is why the Awolowo-Akintola feud still matters. It was not gossip in an agbada. It was an early Nigerian lesson that opposition can die in two ways. It can be strangled from outside by a hostile ruling order. Or, more dangerously, it can decay from within, when conviction gives way to access, when strategy becomes personal survival, when party machinery becomes a theatre of ego. The Western crisis was, in that sense, not only about who should lead. It was about whether opposition should remain an instrument of principle or become a bargaining chip in the market of power.
Kano and Kaduna then enter the story like twin furnaces of northern political memory. Kano carries the old radical grammar of Aminu Kano, NEPU, Sawaba, talakawa politics, the language of emancipation rather than patronage. Oxford’s entry on Aminu Kano notes his struggle against corruption and oppression in the emirate order and his commitment to democratizing Northern Nigeria. The PRP’s own profile, lodged with INEC, explicitly roots itself in NEPU’s legacy and recalls that the PRP had two state governments in the Second Republic: Kaduna and Kano. In other words, both states are not accidental footnotes in the story of Nigerian opposition. They are ancestral terrain.
Then came 1999 and the Fourth Republic, with the PDP arriving not merely as a party but as a vast political weather system. Founded in 1998 and quickly becoming dominant, winning the presidency and legislative majorities in 1999 and retained national control for years. Opposition existed, yes, but it was fragmented, regional, underpowered, and often more symbolic than threatening. That era did not abolish opposition. It domesticated it.
The great interruption came in 2013, when the APC was formed through the merger of major opposition forces. That merger worked because it answered a Nigerian truth older than any campaign slogan: power rarely yields to scattered complaint. It yields to a disciplined coalition. The APC emerged from the merger of ACN, CPC, ANPP, and part of APGA, and in 2015, Buhari’s victory marked the first time an incumbent was defeated and the first inter-party transfer of power in Nigeria’s post-independence history. Reuters described it plainly as a historic democratic transfer. For a brief moment, opposition in Nigeria looked like more than lamentation. It looked like a ladder.
But even that victory carried a warning label. The problem with Nigerian opposition is that once it wins, it often stops being opposition in spirit and becomes merely the next landlord in the same building. An academic review of Nigeria’s democratic journey notes that the APC and PDP share many structural defects, and even cites the broader judgment that little distinguishes the two main parties because both are fluid elite networks with weak ideology. That diagnosis is painful because it explains so much. In Nigeria, opposition too often opposes only until the gates open. After that, the vocabulary changes, but the appetite stays the same.
This is where Kano and Kaduna become especially revealing from 1999 till now. Kano has repeatedly shown a willingness to defy neat national binaries, and in the 2023 election, it backed Rabiu Kwankwaso of the NNPP in the presidential race while also electing Abba Kabir Yusuf of the NNPP as governor. Kaduna told a different but equally interesting story: it voted Atiku Abubakar of the PDP in the presidential contest, yet elected APC’s Uba Sani as governor. CDD West Africa described the 2023 election as unusually fragmented, noting that all four major presidential contenders won at least one state and that states like Kano, Lagos, and Rivers split among three different parties. So, Kano and Kaduna have not been passive spectators in the Nigerian democratic drama. They have been laboratories of resistance, fragmentation, coalition, and contradiction.
And now we arrive at the present crossroads, where the phrase “one-party state” is no longer a tavern exaggeration but a live political argument. Reuters reported in May 2025 that the APC endorsed President Tinubu for a second term while the opposition was widely seen as too divided and weak to mount a serious challenge, with high-profile defections strengthening the ruling party. AP later reported Tinubu’s denial that Nigeria was being turned into a one-party state, even as several governors and federal lawmakers had left opposition parties for the APC. By February 2026, major opposition leaders, including Atiku, Peter Obi, and Amaechi, were jointly rejecting the new Electoral Act, calling it anti-democratic and warning that it could help install a one-party order. Tinubu, for his part, has continued to insist that democracy requires room for the minority to speak.
So, is Nigeria now a one-party state? Not formally. Not yet. There are still multiple parties, multiple ambitions, multiple resentments, and multiple routes to elite reassembly. But that is not the only question that matters. A country can avoid the legal shell of one-party rule and still drift into the political culture of one-party dominance. That drift happens when the ruling party becomes the default shelter for frightened politicians, when defections replace debate, when opposition parties become war zones of internal ego, and when citizens begin to see parties not as platforms of principle but as bus stops for the next powerful convoy. The danger is less a constitutional decree than a democratic evaporation.
This is why the ghosts of Awolowo and Akintola are still standing by the roadside, watching us. Their quarrel warned that opposition without internal discipline can collapse into treachery, and that power at the centre always knows how to exploit a divided house. Kano reminds us that opposition can spring from social memory, from the stubborn dignity of people who do not always vote as ordered. Kaduna reminds us that politics is rarely simple, that a state can host both establishment power and insurgent sentiment in the same electoral season. And the Fourth Republic reminds us that opposition in Nigeria only works when it is more than noise, more than wounded ambition, more than a coalition of temporarily unemployed strongmen.
The real Nigerian danger, then, is not that one party will conquer the entire country by brilliance alone. It is that the opposition will continue to fail by habit. If opposition is only a queue for access, then the ruling party will keep eating its rivals one defection at a time. If, however, opposition rediscovers ideology, internal democracy, regional credibility, and the courage to look different from what it condemns, then the old republic may still whisper a useful lesson into the new one.
Awolowo and Akintola were not just fighting over a party. They were fighting over the soul of the political alternative in Nigeria. That battle never ended—May Nigeria win!
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn




