Technology
Data Storage Market Will Hit CAGR of 14.4% from 2015 to 2025

By Dipo Olowookere
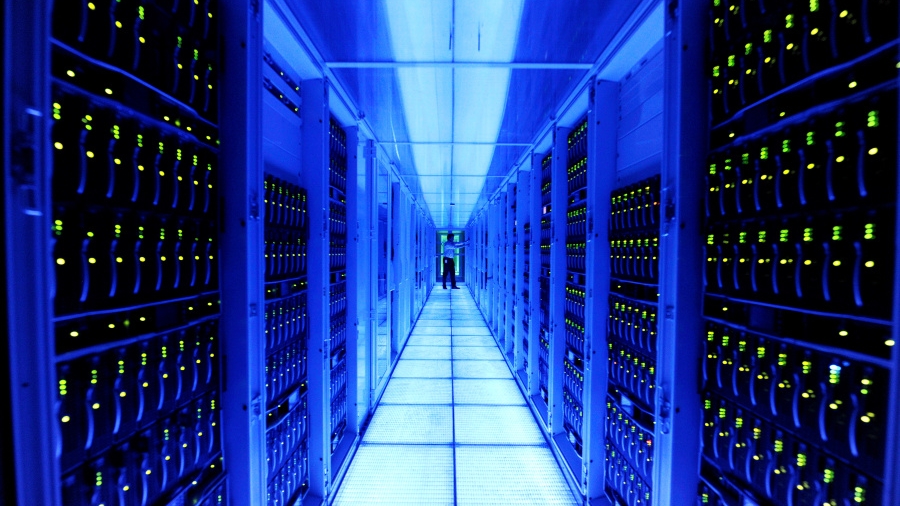
The data storage market is classified into two broad categories: consumer data storage devices and enterprise data storage. Consumer data storage devices include hard disk drives and USB flash drives are used for storing personal data of consumers. Enterprise data storage includes products and services designed for assisting enterprises with cost effective digital information storage solutions. Continuous advancements in information and social technology is one of the primary factors driving growth of the Middle East data storage market currently.
Report Synopsis
Future Market Insights offers a 10-year forecast of the Middle East data storage market between 2015 and 2025. The report considers 2014 as the base year and provides data for the trailing 12 months. In terms of value, the Middle East data storage market is expected to register a CAGR of 14.4% during the forecast period.
Report Description
This research report includes a detailed analysis of the Middle East data storage market for identifying the factors contributing towards growth of the market across different verticals. This study demonstrates the market dynamics and trends in the Middle East regions, which are expected to influence the current nature and future status of the data storage market during the forecast period. A detailed analysis of the value chain further empowers clients to formulate strategies for every stage of their business. The report has been segmented by application into consumer data storage devices and enterprise data storage, on the basis of vertical and end user.
Advancements in information and social technology have paved the way for unabated data growth, which is one of the primary factors contributing to the rise in adoption of advanced enterprise data storage solutions globally. Additionally, small and medium-sized business (SMBs) have begun to leverage actionable information from Big Data and Internet of Things (IoT) enabled devices. Due to this, data storage vendors are introducing latest portfolio of hybrid cloud data protection solutions, in order to offer SMBs as an affordable disaster recovery solution.
This report also includes FMI’s analysis of the key trends, drivers, and restraints that are influencing growth of the Middle East data storage market. The weighted average model is leveraged to identify the impact of the key growth drivers and restraints across various geographies, in order to help clients achieve a categorical view of the market. This report covers trends that are driving each segment and offers analysis and insights regarding the potential of the data storage market in the Middle East regions. The GCC region includes the following countries: UAE, Kuwait, Saudi Arabia, Oman, Qatar and Bahrain; while the Levant region includes Turkey, Israel, Egypt, Lebanon, Jordan and Cyprus. The report also provides key regulations, trends, list of distributers and retailers, and business models followed by key players across each country (mentioned above).
On the basis of consumer data storage devices, the market is segmented into Hard Disk Drive (HDD), Solid State Drives (SSD), memory cards, optical disk and USB flash drives. The Middle East data storage market is categorised further under the enterprise data storage application segment into flash storage and hard disk, cloud based storage, software defined storage and hyper-converged infrastructure. The report also classifies the data storage market by end user (commercial and residential) and vertical (BFSI, healthcare, government, telecom and IT, defence and aerospace, education and other). The report presents a detailed analysis of each segment in terms of market value (US$ Mn). Additionally, it analyses volume (thousand units) contribution by the consumer data storage devices segment, covered under the scope of the Middle East data storage market. In addition to this, a detailed analysis covering the key market trends, absolute dollar opportunity and BPS analysis of the various segments has also been presented.
Given the ever-fluctuating global economy, the report not only forecasts the market on the basis of CAGR, but also analyses the impact of the key parameters for each year over the forecast period. This helps the clients to understand the predictability of the market and to identify the right growth opportunities in the market during the forecast period. Also, a significant feature of this report is the analysis of all vital segments in terms of absolute dollar opportunity. The absolute dollar opportunity is critical in assessing the level of revenue opportunity in the market.
The final section of the data storage market report includes competitive landscape, which is aimed at presenting the client with a dashboard view of the overall market, based on the categories of providers in the value chain, product portfolios, and key differentiating factors. This section is important for gleaning insights about the participants in the market’s ecosystem. Additionally, it enables identification and evaluation of key competitors based on the in-depth assessment of their capabilities and successes in the marketplace. The report includes comprehensive profiles of the providers to evaluate their long-term and short-term strategies, key offerings and recent developments. Key competitors covered in this report include IBM Corporation, Microsoft Corporation, VMware, Inc., Hewlett Packard Enterprise Co., NetApp Inc., Open Text Corp., Sandisk Corporation, Hitachi Data System Corporation, EMC Corporation and Nexenta Systems, Inc.
Research Methodology
In order to evaluate the market size, revenue generated by the data storage vendors has been taken into consideration. Average selling price of each product included as a part of the consumer data storage devices across each country of the Middle East region was considered for estimating market revenue across respective regions. Moreover, market estimates have been analysed keeping in mind different factors, including technology, environment, economic, legal and social. In order to provide correct market forecast statistics, the current market was sized as it forms the basis of the data storage market during the forecast period. Given the characteristics of the market, we triangulated the outcome on the basis of three different types of data, including secondary research, primary research and data from paid databases. Primary research represents the bulk of our research efforts, supplemented by extensive secondary research. Secondary research includes the key players’ product literature, annual reports, press releases and relevant documents, recent trade journals, technical writing, Internet sources, trade associations, agencies and statistical data from government websites. This collated data from primary and secondary data sources is then analysed by the in-house research panel using market research statistical tools.
Technology
LINX Launches 12-month No-Charge Promo in Ghana

By Modupe Gbadeyanka
To develop the country’s internet ecosystem and build a dedicated connectivity community, the London Internet Exchange (LINX) has launched a 12-month no-charge promotion for all services at its new Ghana Internet Exchange Point, LINX Accra.
LINX Accra went live at the end of 2025, providing a regional interconnection point and a platform for networks to meet and exchange traffic, available from PAIX, Onix and the new Digital Realty data centre launched at the end of last year.
As part of its growth drive, LINX Accra aims to attract major global internet carriers and content delivery networks to keep more traffic local to Ghana, building relationships between local networks and encouraging early adoptions through promotion.
A key aspect is growing the local networking and peering community to reduce Ghana’s reliance on international routing, improve latency, and cut costs for networks and end users across the country.
“Ghana’s connectivity ecosystem is growing fast, and our goal, through the promotion, is to remove early barriers and encourage local ISPs to join and exchange traffic from the start.
“We’ve seen in other African markets that once the local community grows, global networks follow, so this is an important step for building community engagement and driving the localisation of internet traffic in Ghana and West Africa,” the Head of Existing Business for LINX, Inga Turner, said.
Ghana is one of West Africa’s fastest-growing digital markets, with over 70 per cent of the country’s 25 million people accessing the internet, and Accra is connected to six submarine cables to provide international connectivity to the country.
The market is also attracting significant data centre investment with new facilities opening every few months.
LINX has had a successful growth in Kenya, building on a similar promotion for LINX Mombasa and LINX Nairobi, which helped establish and expand the connectivity ecosystem, attracting major global networks and content providers to keep traffic local.
Technology
FG to Establish National Cybersecurity Council to Tackle Digital Threats

By Adedapo Adesanya
The federal government has announced plans to establish a national cybersecurity coordination council to strengthen Nigeria’s response to rising digital threats.
In a statement, the Federal Ministry of Communications, Innovation and Digital Economy said the council will serve as a multi-stakeholder platform to improve coordination, intelligence sharing, and collaboration between public and private institutions.
The initiative, championed by the Minister of Communications, Mr Bosun Tijani, aims to enhance Nigeria’s ability to respond to increasingly sophisticated cyber incidents affecting both private companies and public systems.
“The proposed council is envisioned as a non-statutory, multi-stakeholder coordination platform, designed to convene key actors and strengthen partnerships that support efficient coordination, trusted information sharing, and sustained cooperation among institutions responsible for advancing Nigeria’s cybersecurity posture,” the ministry said.
The council will bring together chief information security officers, cybersecurity experts, technology firms, law enforcement agencies, and relevant government institutions.
It will also provide advisory support to the federal government on strategies and frameworks needed to improve national cyber resilience.
“The approach reflects the government’s recognition that modern cyber threats demand collective defence models, trusted threat intelligence sharing, and multi-stakeholder coordination,” the ministry added.
The move follows recent cyber incidents that disrupted operations and highlighted the “increasingly coordinated and sophisticated nature of cyber threats,” signalling the urgent need for stronger national cybersecurity frameworks.
This development comes amid the rising frequency and complexity of cybercrimes, which have made cybersecurity a vital tool that countries must focus on.
Special policies around data breaches, ransomware attacks, and third-party liabilities have come to the fore. While cybersecurity has been historically underutilised in Nigeria, its critical role in mitigating the financial fallout of cybercrimes and threats has taken a new dimension with the adoption of Artificial Intelligence (AI).
Countries are leveraging AI tools to enhance threat detection, automate incident response, and analyse patterns to identify risks early. These AI-driven solutions enable quick and effective responses, improving resilience by detecting anomalies, predicting potential attacks, and mitigating threats before they escalate.
Technology
Airtel Subscriber Base Crosses 650 million, Now World’s Second-Largest Telco

By Modupe Gbadeyanka
Bharti Airtel has crossed 650 million mobile subscribers worldwide to emerge as the world’s second-largest telecommunications firm.
The Indian company has operations in several countries, including Nigeria, where it has continued to scale infrastructure at a pace unmatched in its recent history.
Over the past three years, the telco has increased its national site count from just above 13,000 to nearly 17,200 sites, including more than 1,560 added in the last 12 months.
This expansion deepens capacity in high-demand corridors and extends high-speed coverage to previously underserved regions.
The latest industry data from the Nigerian Communications Commission (NCC) underscores the significance of this growth. As of December 2025, Nigeria recorded 145,141 base stations across 2G, 3G, 4G and 5G layers.
Of this national infrastructure, Airtel accounts for 46,918 base-station layers, reflecting its substantial contribution to the country’s radio access network and its push to absorb rising data consumption.
Nearly 99 per cent of Airtel Nigeria’s sites are now 4G-enabled, positioning the operator as one of the few with a near-ubiquitous high-speed broadband footprint. Thousands of sites have been upgraded for capacity in the past year alone, enabling improved speeds and more stable performance during peak usage.
That expansion underpins Nigeria’s rising internet adoption. According to the latest regulator figures, Nigeria’s internet penetration recently climbed above 50 per cent, with Airtel recording among the largest monthly increases in new internet subscribers, driven by network upgrades across states and rural corridors.
Strategic Connectivity and Redundancy
Airtel is also tackling a critical infrastructure challenge for the Nigerian digital economy: reliance on a single international internet gateway. The company is advancing plans for its second submarine cable internet breakout point at Kwa Ibo in Akwa Ibom State, early in the 2Africa cable system rollout, to provide faster and more resilient national connectivity across regions. This significant investment aligns with global best practices in network diversity and redundancy, ensuring a more stable digital experience for consumers and enterprises alike.
Digital Finance at Scale: SmartCash
Airtel’s digital finance arm, SmartCash, has gained traction in Nigeria’s competitive mobile money ecosystem, now serving over 3 million active users. The platform is supported by an expansive agent network and digital services that lower barriers for everyday financial transactions and savings.
Outstanding Human Touch: Retail Reach
Across Nigeria, Airtel’s retail distribution network stands as one of the sector’s most extensive, with approximately 4,000 exclusive outlets bringing services, support, and products closer to customers in small towns, communities, and high-traffic urban hubs. That footprint drives both access and engagement in a market where localised presence remains a competitive differentiator.
As Nigeria’s digital economy continues to evolve, Airtel is committed to sustained innovation — from expanded fibre backbones and advanced mobile broadband to future-ready services that include satellite-enabled solutions and enterprise-grade digital platforms. These efforts help ensure that connectivity, commerce, and creativity thrive across Nigeria and beyond.
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn

