Technology
The Ultimate Online Privacy Guide

By Douglas Crawford
Introduction
Edward Snowden’s NSA spying revelations highlighted just how much we have sacrificed to the gods of technology and convenience something we used to take for granted, and once considered a basic human right – our privacy.
It is just not just the NSA. Governments the world over are racing to introduce legislation that allows to them to monitor and store every email, phone call and Instant Message, every web page visited, webinar software and every VoIP conversation made by every single one of their citizens.
The press has bandied parallels with George Orwell’s dystopian world ruled by an all-seeing Big Brother about a great deal. They are depressingly accurate.
Encryption provides a highly effective way to protect your internet behavior, communications, and data. The main problem with using encryption is that its use flags you up to organizations such as the NSA for closer scrutiny.
Details of the NSA’s data collection rules are here. What it boils down to is that the NSA examines data from US citizens, then discards it if it’s found to be uninteresting. Encrypted data, on the other hand, is stored indefinitely until the NSA can decrypt it.
The NSA can keep all data relating to non-US citizens indefinitely, but practicality suggests that encrypted data gets special attention.
If a lot more people start to use encryption, then encrypted data will stand out less, and surveillance organizations’ job of invading everyone’s privacy will be much harder. Remember – anonymity is not a crime!
How Secure is Encryption?
Following revelations about the scale of the NSA’s deliberate assault on global encryption standards, confidence in encryption has taken a big dent. So let’s examine the current state of play…
Encryption Key Length
 Key length is the crudest way of determining how long a cipher will take to break. It is the raw number of ones and zeros used in a cipher. Similarly, the crudest form of attack on a cipher is known as a brute force attack (or exhaustive key search). This involves trying every possible combination to find the correct one.
Key length is the crudest way of determining how long a cipher will take to break. It is the raw number of ones and zeros used in a cipher. Similarly, the crudest form of attack on a cipher is known as a brute force attack (or exhaustive key search). This involves trying every possible combination to find the correct one.
If anyone is capable of breaking modern encryption ciphers it is the NSA, but to do so is a considerable challenge. For a brute force attack:
- A 128-bit key cipher has 3.4 x10(38) possible keys. Going through each of them would thousands of operations or more to break.
- In 2011 the fastest supercomputer in the word (the Fujitsu K computer located in Kobe, Japan) was capable of an Rmax peak speed of 10.51 petaflops. Based on this figure, it would take Fujitsu K 1.02 x 10(18) (around 1 billion) years to crack a 128-bit AES key by force.
- In 2016 the most powerful supercomputer in the world is the NUDT Tianhe-2 in Guangzhou, China. Almost 3 times as fast as the Fujitsu K, at 33.86 petaflops, it would “only” take it around a third of a billion years to crack a 128-bit AES key. That’s still a long time, and is the figure for breaking just one key.
- A 256-bit key would require 2(128) times more computational power to break than a 128-bit one.
- The number of years required to brute force a 256-bit cipher is 3.31 x 10(56) – which is about 20000….0000 (total 46 zeros) times the age of Universe (13.5 billion or 1.35 x 10(10) years!

128-bit Encryption
Until the Edward Snowden revelations, people assumed that 128-bit encryption was in practice uncrackable through brute force. They believed it would be so for around another 100 years (taking Moore’s Law into account).
In theory, this still holds true. However, the scale of resources that the NSA seems willing to throw at cracking encryption has shaken many experts’ faith in these predictions. Consequently, system administrators the world over are scrambling to upgrade cipher key lengths.
If and when quantum computing becomes available, all bets will be off. Quantum computers will be exponentially more powerful than any existing computer, and will make all current encryption ciphers and suites redundant overnight.
In theory, the development of quantum encryption will counter this problem. However, access to quantum computers will initially be the preserve of the most powerful and wealthy governments and corporations only. It is not in the interests of such organizations to democratize encryption.
For the time being, however, strong encryption is your friend.
Note that the US government uses 256-bit encryption to protect ‘sensitive’ data and 128-bit for ‘routine’ encryption needs.
However, the cipher it uses is AES. As I discuss below, this is not without problems.
Ciphers
Encryption key length refers to the amount of raw numbers involved. Ciphers are the mathematics used to perform the encryption. It is weaknesses in these algorithms, rather than in the key length, that often leads to encryption breaking.
By far the most common ciphers that you will likely encounter are those OpenVPN uses: Blowfish and AES. In addition to this, RSA is used to encrypt and decrypt a cipher’s keys. SHA-1 or SHA-2 are used as hash functions to authenticate the data.
AES is generally considered the most secure cipher for VPN use (and in general). Its adoption by the US government has increased its perceived reliability, and consequently its popularity. However, there is reason to believe this trust may be misplaced.
NIST
The United States National Institute of Standards and Technology (NIST) developed and/or certified AES, RSA, SHA-1 and SHA-2. NIST works closely with the NSA in the development of its ciphers.
Given the NSA’s systematic efforts to weaken or build backdoors into international encryption standards, there is every reason to question the integrity of NIST algorithms.
NIST has been quick to deny any wrongdoing (“NIST would not deliberately weaken a cryptographic standard”). It has also has invited public participation in a number of upcoming proposed encryption-related standards in a move designed to bolster public confidence.
The New York Times, however, has accused the NSA of introducing undetectable backdoors, or subverting the public development process to weaken the algorithms, thus circumventing NIST-approved encryption standards.
News that a NIST-certified cryptographic standard – the Dual Elliptic Curve algorithm (Dual_EC_DRGB) had been deliberately weakened not just once, but twice, by the NSA destroyed pretty much any existing trust.

That there might be a deliberate backdoor in Dual_EC_DRGB had already been noticed before. In 2006 researchers at the Eindhoven University of Technology in the Netherlands noted that an attack against it was easy enough to launch on ‘an ordinary PC.’ Microsoft engineers also flagged up a suspected backdoor in the algorithm.
Despite these concerns, where NIST leads, industry follows. Microsoft, Cisco, Symantec and RSA all include the algorithm in their products’ cryptographic libraries. This is in large partbecause compliance with NIST standards is a prerequisite to obtaining US government contracts.
NIST-certified cryptographic standards are pretty much ubiquitous worldwide throughout all areas of industry and business that rely on privacy (including the VPN industry). This is all rather chilling.
Perhaps because so much relies on these standards, cryptography experts have been unwilling to face up to the problem.
Perfect Forward Secrecy
One of the revelations in the information provided by Edward Snowden is that “another program, code-named Cheesy Name, was aimed at singling out SSL/TLS encryption keys, known as ‘certificates,’ that might be vulnerable to being cracked by GCHQ supercomputers.”
That these certificates can be “singled out” strongly suggests that 1024-bit RSA encryption (commonly used to protect the certificate keys) is weaker than previously thought. The NSA and GCHQ could therefore decrypt it much more quickly than expected.
In addition to this, the SHA-1 algorithm widely used to authenticate SSL/TLS connections is fundamentally broken. In both cases, the industry is scrambling fix the weaknesses as fast as it can. It is doing this by moving onto RSA-2048+, Diffie-Hellman, or Elliptic Curve Diffie-Hellman (ECDH) key exchanges and SHA-2+ hash authentication.
What these issues (and the 2014 Heartbleed Bug fiasco) clearly highlight is the importance of using perfect forward secrecy (PFS) for all SSL/TLS connections.
This is a system whereby a new and unique (with no additional keys derived from it) private encryption key is generated for each session. For this reason, it is also known as an ephemeral key exchange.
Using PFS, if one SSL key is compromised, this does not matter very much because new keys are generated for each connection. They are also often refreshed during connections. To meaningfully access communications these new keys would also need to be compromised. This makes the task so arduous as to be effectively impossible.
Unfortunately, it is common practice (because it’s easy) for companies to use just one private encryption key. If this key is compromised, then the attacker can access all communications encrypted with it.
OpenVPN and PFS
The most widely used VPN protocol is OpenVPN. It is considered very secure. One of the reasons for this is because it allows the use of ephemeral keys.
Sadly this is not implemented by many VPN providers. Without perfect forward secrecy, OpenVPN connections are not considered secure.
It is also worth mentioning here that the HMAC SHA-1 hashes routinely used to authenticate OpenVPN connections are not a weakness. This is because HMAC SHA-1 is much less vulnerable to collision attacks than standard SHA-1 hashes. Mathematical proof of this is available in this paper.
The Takeaway – So, is Encryption Secure?
To underestimate the NSA’s ambition or ability to compromise all encryption is a mistake. However, encryption remains the best defense we have against it (and others like it).
To the best of anyone’s knowledge, strong ciphers such as AES (despite misgivings about its NIST certification) and OpenVPN (with perfect forward secrecy) remain secure.
As Bruce Schneier, encryption specialist, fellow at Harvard’s Berkman Center for Internet and Society, and privacy advocate famously stated,
“Trust the math. Encryption is your friend. Use it well, and do your best to ensure that nothing can compromise it. That’s how you can remain secure even in the face of the NSA.”
Remember too that the NSA is not the only potential adversary. However, most criminals and even governments have nowhere near the NSA’s ability to circumvent encryption.
The Importance of End-to-end Encryption
End-to-end (e2e) encryption means that you encrypt data on your own device. Only you hold the encryption keys (unless you share them). Without these keys, an adversary will find it extremely difficult to decrypt your data.

Many services and products do not use e2e encryption. Instead they encrypt your data and hold the keys for you. This can be very convenient, as it allows for easy recovery of lost passwords, syncing across devices, and so forth. It does mean, however, that these third parties could be compelled to hand over your encryption keys.
A case in point is Microsoft. It encrypts all emails and files held in OneDrive (formerly SkyDrive), but it also holds the encryption keys. In 2013 it used these to unlock the emails and files of its 250 million worldwide users for inspection by the NSA.
Strongly avoid services that encrypt your data on their servers, rather than you encrypting your own data on your own machine.
HTTPS
Although strong encryption has recently become trendy, websites have been using strong end-to-end encryption for the last 20 years. After all, if websites were not secure, then online shopping or banking wouldn’t be possible.
The encryption protocol used for this is HTTPS, which stands for HTTP Secure (or HTTP over SSL/TLS). It is used for websites that need to secure users’ communications and is the backbone of internet security.
When you visit a non-secure HTTP website, data is transferred unencrypted. This means anyone watching can see everything you do while visiting that site. This includes your transaction details when making payments. It is even possible to alter the data transferred between you and the web server.
With HTTPS, a cryptographic key exchange occurs when you first connect to the website. All subsequent actions on the website are encrypted, and thus hidden from prying eyes. Anyone watching can see that you have visited a certain website, but cannot see which individual pages you read, or any data transferred.
For example, the BestVPN.com website is secured using HTTPS. Unless you are using a VPN while reading this web page, your ISP can see that you have visited www.bestvpn.com, but cannot see that you are reading this particular article. HTTPS uses end-to-end encryption.
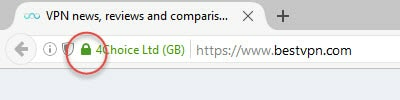
It is easy to tell if you visit a website secured by HTTPS – just look for a locked padlock icon to the left of the main URL/search bar.
There are issues relating to HTTPS, but in general it is secure. If it wasn’t, none of the billions of financial transactions and transfers of personal data that happen every day on the internet would be possible. The internet itself (and possibly the world economy!) would collapse overnight.
For a detailed discussion on HTTPS, please see here.
Metadata
An important limitation to encryption is that it does not necessarily protect users from the collection of metadata.
Even if the contents of emails, voice conversations, or web browsing sessions cannot be readily listened in on, knowing when, where, from whom, to whom, and how regularly such communication takes place can tell an adversary a great deal. This is a powerful tool in the wrong hands.
For example, even if you use a securely encrypted messaging service such as WhatsApp, Facebook will still be able to tell who you are messaging, how often you message, how long you usually chat for, and more. With such information, it would be easy to discover that you were having an affair, for example.
Although the NSA does target individual communications, its primary concern is the collection of metadata. As NSA General Counsel Stewart Baker has openly acknowledged,
“Metadata absolutely tells you everything about somebody’s life. If you have enough metadata, you don’t really need content.“
Technologies such as VPNs and Tor can make the collection of metadata very difficult. For example, an ISP cannot collect metadata relating to the browsing history of customers who use a VPN to hide their online activities.
Note, though, that many VPN providers themselves log some metadata. This should be a consideration when choosing a service to protect your privacy.
Please also note that mobile apps typically bypass any VPN that is running on your device, and connect directly to their publishers’ servers. Using a VPN, for example, will not prevent WhatsApp sending metadata to Facebook.
Identify Your Threat Model
When considering how to protect your privacy and stay secure on the internet, carefully consider who or what worries you most. Defending yourself against everything is almost impossible. And any attempt to do so will likely seriously degrade the usability (and your enjoyment) of the internet.
Identifying to yourself that being caught downloading an illicit copy of Game of Thrones is a bigger worry than being targeted by a crack NSA TAO teamfor personalized surveillance is a good start. It will leave you less stressed, with a more useable internet and with more effective defenses against the threats that really matter to you.
Of course, if your name is Edward Snowden, then TAO teams will be part of your threat model…
I will discuss steps you should take to help identify your threat model in an upcoming article on BestVPN.com. In the meantime, this article does a good job of introducing the basics.
Use FOSS Software
 The terrifying scale of the NSA’s attack on public cryptography, and its deliberate weakening of common international encryption standards, has demonstrated that no proprietary software can be trusted. Even software specifically designed with security in mind.
The terrifying scale of the NSA’s attack on public cryptography, and its deliberate weakening of common international encryption standards, has demonstrated that no proprietary software can be trusted. Even software specifically designed with security in mind.
The NSA has co-opted or coerced hundreds of technology companies into building backdoors into their programs, or otherwise weakening security in order to allow it access. US and UK companies are particularly suspect, although the reports make it clear that companies across the world have acceded to NSA demands.
The problem with proprietary software is that the NSA can fairly easily approach and convince the sole developers and owners to play ball. In addition to this, their source code is kept secret. This makes it easy to add to or modify the code in dodgy ways without anyone noticing.
The best answer to this problem is to use free open source software (FOSS). Often jointly developed by disparate and otherwise unconnected individuals, the source code is available to everyone to examine and peer-review. This minimizes the chances that someone has tampered with it.
Ideally, this code should also be compatible with other implementations, in orderto minimize the possibility of a backdoor being built in.
It is, of course, possible that NSA agents have infiltrated open source development groups and introduced malicious code without anyone’s knowledge. In addition, the sheer amount of code that many projects involve means that it is often impossible to fully peer-review all of it.
Despite these potential pitfalls, FOSS remains the most reliable and least likely to be tampered with software available. If you truly care about privacy you should try to use it exclusively (up to and including using FOSS operating systems such as Linux).
Steps You Can Take to Improve Your Privacy
With the proviso that nothing is perfect, and if “they” really want to get you “they” probably can, there are steps you can take to improve your privacy.
Pay for Stuff Anonymously
One step to improving your privacy is to pay for things anonymously. When it comes to physical goods delivered to an actual address, this isn’t going to happen. Online services are a different kettle of fish, however.
It is increasingly common to find services that accept payment through Bitcoin and the like. A few, such as VPN service Mullvad, will even accept cash sent anonymously by post.
Bitcoin
Bitcoin is a decentralized and open source virtual currency that operates using peer-to-peer technology (much as BitTorrent and Skype do). The concept is particularly revolutionary and exciting because it does not require a middleman to work (for example a state-controlled bank).
Whether or not Bitcoins represent a good investment opportunity remains hotly debated, and is not within the remit of this guide. It is also completely outside of my area of expertise!
Source: Bestvpn.com
Technology
Lagos Eyes 250MW Data Centre Capacity by 2030
By Adedapo Adesanya
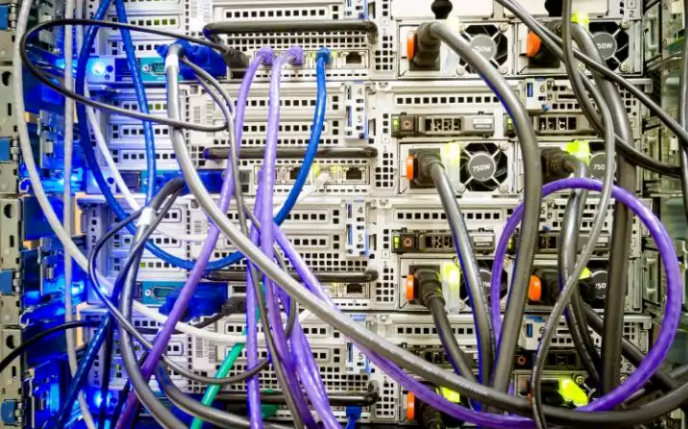
The Lagos State government plans to expand the city’s data centre capacity to over 250 megawatts (MW) by 2030 as part of efforts to strengthen its digital infrastructure ecosystem.
This was disclosed by the state’s Commissioner for Innovation, Science, and Technology, Mr Olatubosun Alake, at the launch of the Kasi Cloud LOS1 data centre facility in Lekki. Nigeria Sovereign Investment Authority (NSIA) invested in Kasi Cloud through an $8 million convertible loan note in 2021.
Mr Alake said Lagos already hosts nearly three-quarters of Nigeria’s commercial data centre capacity, adding that the government intends to expand its infrastructure footprint significantly over the next five years.
“There are about 146 additional megawatt data centres planned in the pipeline,” he said. “We envisage that by 2030, we would have over 250 megawatts of data centre capacity in Lagos, three times the current capacity growth.”
The expansion comes as demand for cloud services, AI computing power, and local data storage continues to grow across Nigeria’s digital economy, with Lagos at the forefront, housing thousands of businesses and startups.
Mr Alake said the Kasi Cloud facility represents Lagos’ entry into “large-scale hyperscale AI infrastructure,” signalling the state’s ambition to evolve beyond being known primarily as a startup hub into a major centre for digital infrastructure and AI computing.
“Lagos is no longer simply a startup city,” he said. “It is an infrastructure city.”
The Kasi LOS1 facility is designed as a 40MW hyperscale data centre campus, beginning operations with an initial 7.2MW IT load.
According to Mr Alake, the facility includes advanced GPU computing infrastructure powered by Nvidia H100 and H200 chips, alongside liquid cooling systems and cloud infrastructure services designed to support AI workloads.
The Lagos State government believes such infrastructure will become critical as AI adoption accelerates globally.
Mr Alake said the state is investing in fibre optic networks, smart city technologies, university innovation programmes, and digital government systems to prepare for the transition.
“The AI economy is going to require hundreds of megawatts,” he said. “The market has already made its decision about where digital infrastructure belongs.”
On his part, Mr Johnson Agbogun, co-founder and chief executive officer of Kasi Cloud, said the project was built to reduce Nigeria’s dependence on foreign cloud infrastructure and give African businesses more control over how their data and AI systems are developed.
“Nigerian enterprises are currently spending $850 million every year on foreign cloud infrastructure,” he said. “Every naira spent abroad on cloud and AI infrastructure helps build capabilities somewhere else.”
He added that the facility runs GPU-powered AI workloads from local enterprises and described the Lekki campus as “the beginning of Nigeria’s AI factory.”
“As artificial intelligence reshapes economies globally, the nations that control their own compute infrastructure and data will be the ones positioned to lead,” added Mr Kolawole Owodunni, NSIA’s Executive Director and Chief Information Officer.
Technology
Google I/O 2026: 4 Major Updates That Are Changing How Google Search Works

The goal of Google Search has always been simple: to help you ask anything on your mind. Whether it is a quick fact to help with your daily hustle or a complex question about starting a new business, Nigerians rely on Search every single day.
Over the last year, Google has rapidly reimagined what Search can do with AI. The momentum has been incredible—just one year after its debut, AI Mode has surpassed one billion monthly users globally. As people have realised just how much more Search can do for them, they are searching more than ever before, reaching an all-time high in search queries last quarter. Today at Google I/O, Google shared the next step in its journey to bring together the best of a search engine with the best of AI.
To power this next chapter, Google is officially upgrading Search with Gemini 3.5 Flash as the new default model in AI Mode for everyone worldwide. Delivering sustained frontier performance for agents and coding, Gemini 3.5 Flash is the engine driving the new era of AI-powered Search. Because curiosity doesn’t always fit into standard keywords, this powerful AI model is transforming Search from a tool that simply finds information into an intelligent platform capable of reasoning, monitoring the web, and executing complex tasks on your behalf.
Here is a look at the four biggest AI-powered announcements coming to Google Search:
1. A Completely Reimagined Search Box
Google is introducing the biggest upgrade to its Search box in over 25 years. Now completely reimagined with AI, the new intelligent Search box dynamically expands to give you the space to describe exactly what you need. It goes beyond simple autocomplete by anticipating your intent and helping you phrase your questions. You are no longer limited to typing; you can now search using text, images, files, videos, or even Chrome tabs as inputs. Additionally, Google is making it easier to ask follow-up questions directly from an AI Overview, flowing naturally into a conversational back-and-forth where your context stays with you as you explore.
2. New Search Agents That Work in the Background
We are entering the era of Search agents, where you can create and manage multiple AI agents directly in Search. Google is launching “Information agents” that operate in the background 24/7. These agents intelligently scan the web—alongside fresh data on finance, shopping, and sports—to monitor for changes related to your specific questions. For example, if you are house hunting, your agent will continuously scan the market and notify you the moment a listing matches your exact criteria. Furthermore, Search is expanding its agentic booking capabilities; you can soon share specific criteria (like a late-night private karaoke room) and Search will pull the latest pricing and links to finish booking. For certain categories, Google can even call businesses on your behalf.
3. Custom Mini-Apps and Visuals Built Just for You
Search is no longer just returning links; it is now building the ideal response in the perfect format for your query entirely on the fly. By bringing the power of Google Antigravity and the agentic coding capabilities of Gemini 3.5 Flash into Search, users will get a custom “Generative UI.” This means Search can design custom layouts, interactive visuals, tables, graphs, or simulations in real-time. But it goes a step further: if you have an ongoing task, like establishing a new health routine, Search can actually code a custom fitness tracker or mini-app for you. These custom dashboards tap into real-time sources like live maps and weather, giving you a personalised tracker you can return to again and again.
4. Expanded Personal Intelligence Without a Subscription
For AI to be truly helpful, it shouldn’t just know the world’s information—it should understand your personal context, too. To achieve this, Google is expanding Personal Intelligence in AI Mode to more people in nearly 200 countries and territories across 98 languages. Crucially, this is being rolled out with no subscription required. Users can securely connect apps like Gmail, Google Photos, and soon Google Calendar directly to Search. Designed with transparency and choice at its heart, this allows you to safely ask Search to find information buried in your own personal files, always keeping you in complete control of your connected data.
Technology
Fibre Cuts: Expert Blames Road Construction for 60% of Network Outages

By Modupe Gbadeyanka
The chief executive of Dimensions Data Limited, Mr Gbenga Olabiyi, has blamed road construction for 60 per cent of network outages caused by fibre cuts.
Speaking recently at the National Dig-Once Policy Forum, which marked the 8th Policy Implementation Assisted Forum (PIAFo), he drew attention to the gap between the infrastructure Nigeria has and what it can actually deliver if a coordinated framework is adopted.
“Nigeria currently has about 35,000 kilometres of fibre in the ground, yet only 16 per cent of Nigerians are connected to it. Broadband penetration stands at 45 per cent. Lagos alone has a penetration rate of over 70 per cent,” Mr Olabiyi said.
He emphasised that the failure to address the missing fibre link over the years has led to saturation of connectivity in urban centres, while the hinterlands are left either unconnected or poorly served.
At the same programme, convened by Mr Omobayo Azeez, stakeholders in the telecommunications sector called for the adoption of the dig-once policy to lower the costs of fibre deployment, reduce infrastructure damage, improve safety, and shorten rollout timelines.
Quoting the Nigerian Communications Commission (NCC), it was noted that of the 50,000 fibre cut incidents recorded in a year, about 30,000, which represents 60 per cent, occurred during road construction and rehabilitation.
Stakeholders thus called for a review of existing road construction and building codes to accommodate the installation of fibre conduits in the original design standard of the infrastructure planning.
“What Dig-Once offers is an opportunity to correct this,” the president of the Association of Telecommunication Companies of Nigeria, Mr Tony Emoekpere, stated.
He added that even operators frequently damage one another’s cables during repeated digging, thus increasing repair costs and service disruptions.
The Deputy Director of Strategic Business Initiatives at ipNX Nigeria Limited, Mr Segun Okuneye, said under the dig-once policy, road contractors should install ducts during construction.
He said the repeated excavation of the road leads to incessant destruction of existing infrastructure and triggers service blackouts with operators bearing additional costs of repair of replacing the fibre.
Also, the chairman of the Association of Licensed Telecom Operators of Nigeria (ALTON), Mr Gbenga Adebayo, said operators should focus not just on digging once but on eliminating unnecessary digging altogether by sharing existing infrastructure and jointly replacing legacy cables.
“Early fibres laid 15 to 20 years ago are now ageing, and the industry needs a plan to replace them without everyone digging the same routes again,” he said.
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn



1 Comment