Technology
Salesforce Unveils Conversational AI Assistant Einstein Copilot
By Modupe Gbadeyanka
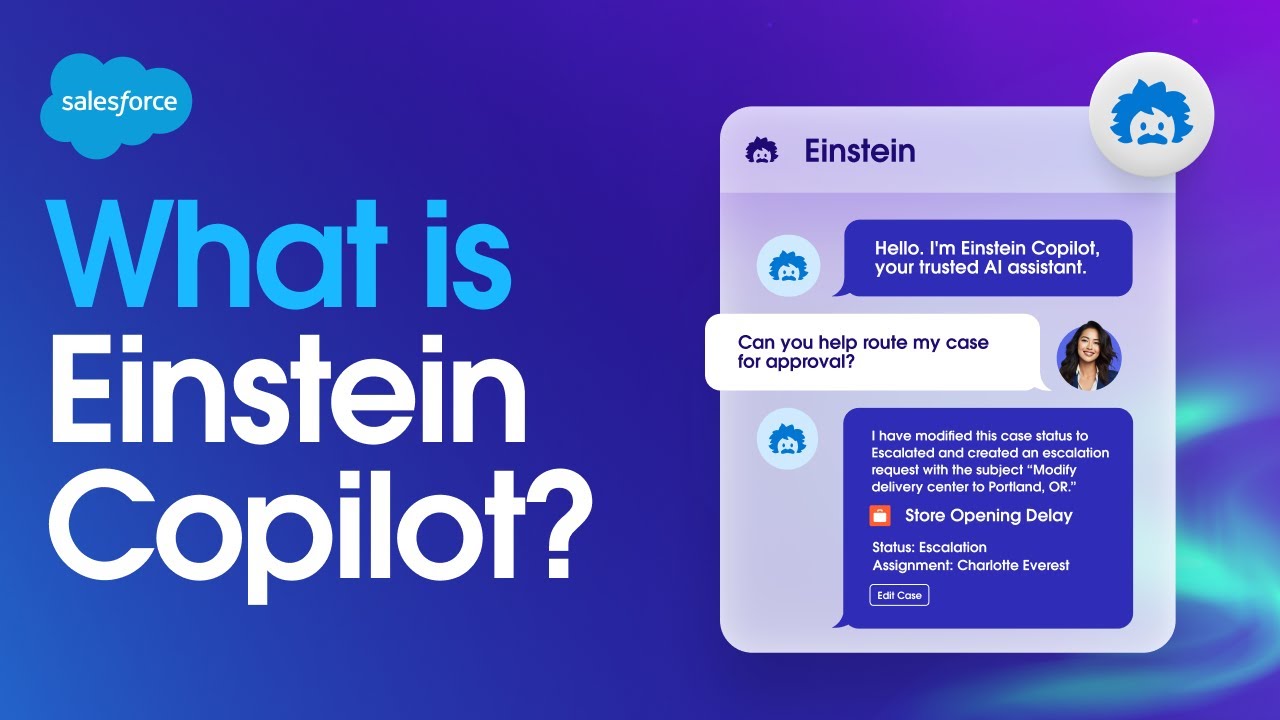
A new customisable, conversational, and generative AI assistant for CRM, Einstein Copilot, has been launched by Salesforce.
The system was unveiled at the Mobile World Congress in Barcelona, Spain, and it will use adequate company data to generate useful responses.
The Einstein Copilot enables Salesforce customers to generate responses using their private and trusted data, while maintaining strict data governance and without requiring expensive AI model training.
As a result, Einstein Copilot can answer questions, summarise content, create new content, interpret complex conversations, and dynamically automate tasks on behalf of a user, all from a single, consistent user experience embedded directly within Salesforce’s AI CRM applications.
This is made possible by combining a conversational UI, a foundational large language model, and trusted company data that enables Salesforce users to tap into the power of generative AI and interact with their applications in entirely new ways.
“AI is the single most important moment in the history of our industry. It will deepen customer relationships, increase productivity and drive higher margins at every company,” said Marc Benioff, Chair & CEO, Salesforce. “Our new Einstein Copilot brings together an amazing intuitive interface for interacting with AI, world-class AI models and above all deep integration of the data and metadata needed to benefit from AI. Einstein Copilot is the only copilot with the ability to truly understand what is going with your customer relationships.”
Einstein Copilot grounds its responses with trusted business data from Data Cloud to provide the necessary context for the highest quality outputs. This allows Einstein Copilot to generate more precise and tailored responses based on trusted company data.
It comes with a library of out-of-the-box actions – pre-programmed capabilities, automated responses, or business tasks performed by Einstein Copilot – that the AI can perform for the user when prompted.
Actions can be combined to execute dynamic multi-step plans. For example, a customer service agent can ask Einstein Copilot to close a case and open a sales opportunity or sell an add-on, and Einstein Copilot will understand the user’s intent and can execute the task — or tasks — in the flow of the service experience. With Einstein Copilot there are no silos between applications or data.
Technology
Nigeria, Finland Strengthen Ties on Digital Economy

By Adedapo Adesanya
The Nigerian government and the Republic of Finland have formalised a strategic partnership on digitalisation and innovation, signing a Memorandum of Understanding (MoU) aimed at expanding economic activities and strengthening cooperation in the digital sector.
The agreement was signed in Abuja by the Minister of Communications, Innovation and Digital Economy, Mr Bosun Tijani, and Mr Jarno Syrjälä, Under‑Secretary of State (International Trade) at Finland’s Ministry for Foreign Affairs.
According to a statement from the Special Assistant on Media and Communications to the communications minister, Mr Isime Esene, the MoU will establish a framework for collaboration across key areas, including digital government, emerging technologies, digital public infrastructure, cybersecurity, innovation ecosystems, and capacity building.
Mr Tijani described the signing as “an important step in strengthening the partnership between both countries as we work to build a more inclusive, innovation-driven digital economy.”
“This agreement is a significant next step following our engagements in Helsinki in February, where we met with key stakeholders, including Finnvera and Finnfund, and held productive discussions on advancing collaboration around digital infrastructure, the Data Exchange Platform, and opportunities for Finnish participation in Project Bridge.”
The Minister emphasised that the partnership would “unlock meaningful opportunities for both countries, enabling us to leverage digital transformation as a catalyst for sustainable growth and shared prosperity.”
Echoing this optimism, Mr Syrjälä said: “Finland is very pleased to deepen its partnership with Nigeria in building resilient, secure, and human‑centric digital societies. Digitalisation is at its best when it empowers people, strengthens trust, and creates new opportunities for innovation.”
“Nigeria is a key partner for Finland in Africa, and this MoU provides a strong basis for concrete cooperation between our governments, institutions, and private sectors. Together, we can advance digital solutions that are interoperable, future‑fit, and beneficial to both our nations,” he added.
Technology
Meta Launches AI Support Assistant on Facebook, Instagram
By Aduragbemi Omiyale
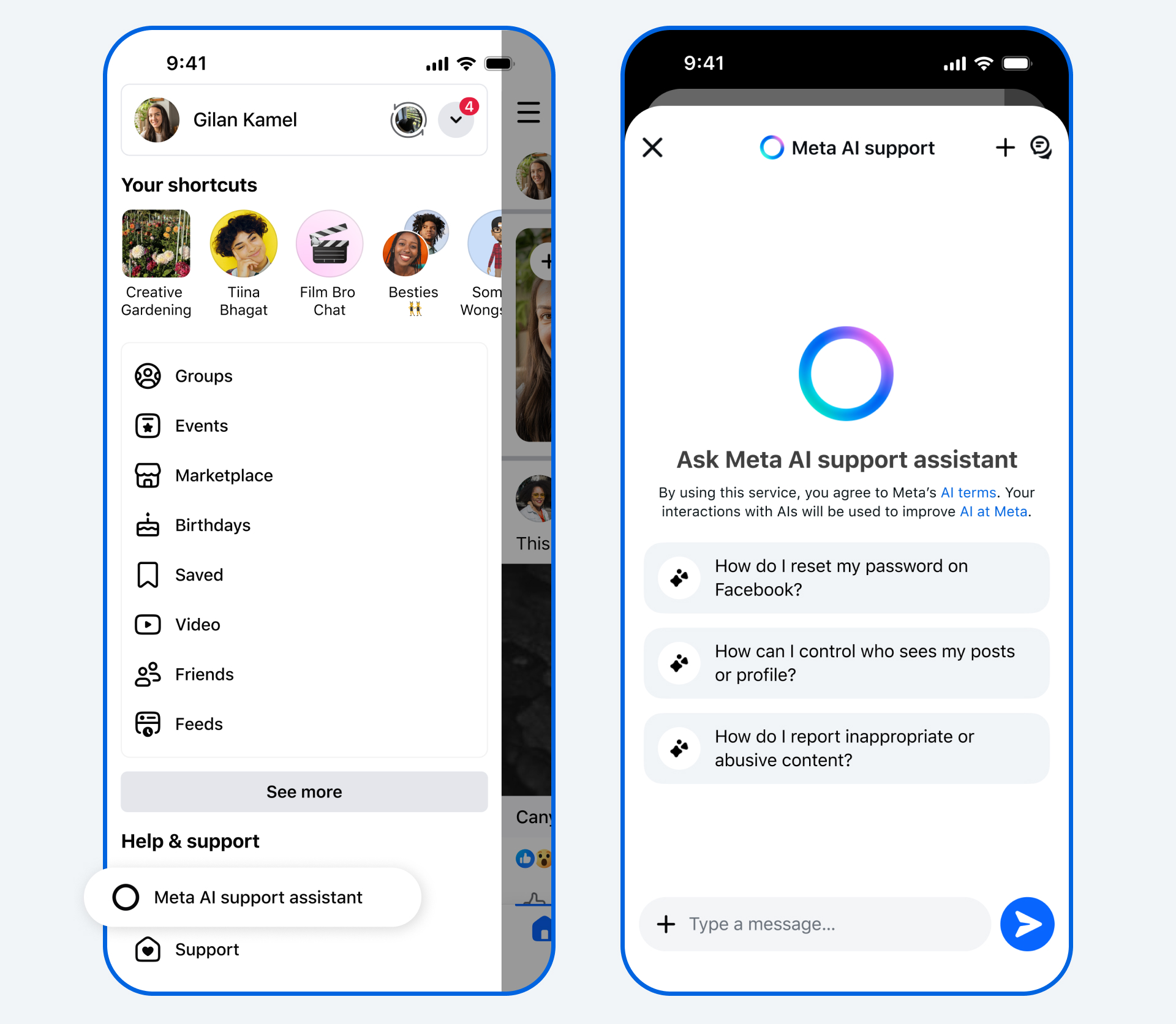
New Artificial Intelligence (AI) tools designed to provide support for users of its applications have been launched by Meta.
The AI Support Assistant will work on the Facebook and Instagram apps, the company said in a statement.
The tools will help users to receive reliable and action-oriented assistance when needed.
In December, the Meta AI support assistant, a tool designed to provide reliable, 24/7 support for nearly any support issue at any time, was previewed.
Now, Meta is rolling it out globally on the Facebook and Instagram apps for iOS and Android, and within Help Centre on Facebook and Instagram on desktop, with even more capabilities and ways to help.
The new Meta AI support assistant is designed to help resolve account problems from start to finish. It offers answers for any question, like notification settings or new features, and can also take action for users on a growing set of requests directly within Facebook and, in the future, on Instagram.
The feature can report scams, impersonation accounts, or problematic content, make it easier to see why content was taken down, provide appeal options, track what happens next, manage privacy settings, reset passwords, and update profile settings.
The Meta AI support assistant can respond to requests typically in under five seconds, dramatically reducing wait times compared to traditional help centre searches or seeking answers on external websites.
“The Meta AI support assistant is a major step in our work to deliver stronger support on our apps. In fact, among people who have provided feedback, the majority report a positive experience with the Meta AI support assistant. It’s rolling out now in all languages supported by Facebook and Instagram for support topics.
“We’re continuing to invest in AI- powered tools to make support more accessible, reliable, and effective — and we’ll keep evolving the Meta AI support assistant as more people use it and as the technology advances, so it continues to improve over time,” the organisation disclosed.
Meta has also deployed AI to improve content enforcement to help users reduce the chance that scammers trick people into giving away their login details, ultimately finding and mitigating 5,000 scam attempts per day that no existing review team had caught before.
Meta said over the next few years, it would be deploying these more advanced AI systems across its apps once they consistently perform better than its current methods of content enforcement, transforming its approach.
“As we do this, we’ll reduce our reliance on third-party vendors for content enforcement and focus on strengthening our internal systems and workforce.
“While we’ll still have people who review content, these systems will be able to take on work that’s better-suited to technology, like repetitive reviews of graphic content or areas where adversarial actors are constantly changing their tactics, such as with illicit drug sales or scams,” it stated.
Technology
Facebook Offers New Tools to Report Impersonation, Removes 20 million Accounts

By Modupe Gbadeyanka
As part of its commitment to celebrating and rewarding creativity, Facebook has updated its guidance, with clear definitions of what counts as original and unoriginal content.
In a message on Monday, the social media platform said it was offering content creators new tools to report impersonation.
Launched last year, the content protection tool is expanding beyond detecting reel matches across Meta platforms to now also flag potential impersonation.
Creators can take action on content theft and easily submit impersonation reports all in one place.
Facebook, in the statement received by Business Post, said creators can check for access to content protection in their professional dashboard or apply for access here.
The platform also disclosed that in 2025, it removed over 20 million accounts impersonating large content creators, and impersonation reports related to large content creators dropped by 33 per cent.
Further, Facebook is deprioritising unoriginal content by making sure they do not perform well on its platform.
It noted that content that is duplicated from other sources or makes low-value changes to someone else’s content may see significantly reduced reach, and accounts that primarily post unoriginal content may lose eligibility for recommendations and monetisation.
It was emphasised that “these changes provide creators who post original content with greater reach and monetisation opportunities, provide stronger protections for their work, and reduce the reach of unoriginal content.”
-

 Feature/OPED6 years ago
Feature/OPED6 years agoDavos was Different this year
-
Travel/Tourism10 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz3 years ago
Showbiz3 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking8 years ago
Banking8 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy3 years ago
Economy3 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking3 years ago
Banking3 years agoSort Codes of UBA Branches in Nigeria
-

 Banking3 years ago
Banking3 years agoFirst Bank Announces Planned Downtime
-

 Sports3 years ago
Sports3 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn